
Cybersecurity in Tamil | இணைய உலகின் தகவல் திருட்டின் ரட்சகன் CYBER SECURITY
Cybersecurity in Tamil:
நாம் தற்பொழுது வாழ்ந்து கொண்டிருக்கும் காலமானது Digital Society ஆகும். உணவை Order செய்வது முதல் Room Booking சேவை வரை தற்பொழுது இணையத்தின் சேவையே தேவையாக உள்ளது. ஆகையால் நாம் தகவல்கள் அனைத்தையும் Cloud Serverல் சேகரித்து வைக்கிறோம். இதனை பயன்படுத்தி இணைய திருடர்கள் அனைவரும் Malwares மற்றும் Virus பயன்படுத்தி தகவல் திருட்டில் ஈடுபடுகிறார்கள். ஏனென்றால் Ipaddress எனப்படும் நமது வலைத்தள முகவரி அனைவரும் பார்க்கும்படி இருப்பதால் அவர்கள் அதை வைத்து இணைய திருட்டில் ஈடுபடுவார்கள்.
Cybersecurity என்பது இணையத்தில் எவ்வாறு தகவல் திருட்டு நடைபெறுகிறது என்னென்ன வழிகளில் நடைபெறுகிறது அதை எவ்வாறு சரி செய்யலாம் போன்றவற்றை பற்றி குறிப்பதாகும். இந்த தகவல் திருட்டை தடுக்க என்னென்ன தொழில்நுட்பம் இருக்கிறது போன்றவற்றை பற்றியும் குறிப்பிடுவதாகும். Cybersecurity என்பது ஒரு வகையான Online service ஆகும் இது ஆன்லைன் தகவல்களை எவ்வாறு பாதுகாப்பாக வைத்து கொள்ளலாம் என்று உதவுகிறது. தற்காலத்தில் மக்கள் அனைவரும் இணையத்தில் இணைந்துள்ளோம் ஆகையால் பலவகையான பாதுகாப்பு அச்சுறுத்தல்கள் ஏற்படுகிறது. இந்த பாதுகாப்பு அச்சுறுத்தல்களிலிருந்து இணைய பயனாளர்களை பாதுகாக்கும் தொழில்நுட்பமே இந்த Cybersecurity ஆகும்.

Cyber Securityன் முக்கிய நோக்கமா கீழ்கண்டவற்றை தடுப்பதை கூறலாம்.
i) Unauthorized Modification(அனுமதிபெறாத மாற்றம்)
ii) Unauthorized Deletion(அனுமதிபெறாத அழிப்பு)
iii) Unauthorized Access(அனுமதிபெறாத பரிவர்த்தனை)
Cyber என்ற வார்த்தையே தகவல் தொழில்நுட்பம், இணையம் மற்றும் விர்சுவல் தொழில்நுட்பம் போன்ற அனைத்தின் கலவையாகும். Cybersecurityன் தேவையானது மிகவும் இன்றியமையாததாகும் இது பொதுவாக தகவல் திருட்டை தடுக்கிறது உதாரணத்திற்கு ஒரு நபர் ஒரு நிறுவனத்தின் தகவல்களை இணையத்தில் திருடி மற்றொரு நிறுவனத்திற்கு கொடுக்கலாம் அல்லது அந்த சம்பத்தப்பட்ட நிறுவனத்தை தொடர்பு கொண்டு அவர்களை பணம் கேட்டு மிரட்டலாம் அல்லது RANSOMWARE போன்ற வைரஸ்களை அனுப்பி தகவல்கள் அனைத்தையும் திருடலாம் இவ்வாறாக அந்த நிறுவனத்திற்கு மிகவும் மோசமான இழப்புகளை ஏற்படுத்தலாம்.
இந்த Cybersecurityன் பாதுகாப்பு அச்சுறுத்தல்களுக்கு காரணமானவைகள்:-
ii) Malware
iii) Trojan Horse
v) Password cracking
vi) Phishing
vii) DDOS Threat
viii) Man in the Middle
ix) Drive by Download
வைரஸ் என்பது முதலில் ஒரு வகையான கணினி புரோக்ராமேயாகும் அது உங்களுடைய கணினியில் உங்கள் விருப்பம் இல்லாமலேயே இயங்கக்கூடியதாகும். இந்த வகையான வைரஸ்கள் அனைத்துமே தகவல்களை திருடுவதற்கு பயன்படுவதேயாகும். இவைகள் அனைத்தும் பெண்டிரைவ் மூலமாகவோ அல்லது இணையத்தின் மூலமாகவோ தங்களை வந்தடைகிறது. இதனை தடுப்பதற்கு தாங்கள் பாதுகாப்பான Antivirusகளை நிறுவியிருந்தால் இது போன்ற பிரச்சனைகளை பெரும்பாலும் தடுக்கலாம்.
Hackers என்பவர்கள் இணையத்தில் நடக்கும் இரு நபர்களுக்கிடையே பண பரிவர்த்தனை மற்றும் அவர்களின் முக்கியமான உரையாடல் போன்றவற்றை பற்றி அவர்களுக்கே தெரியாமல் கட்டுப்படுத்துபவராகும்.
இங்கே இணையத்தை பொறுத்தவரை மூன்று விதமான Hackersகள் காணப்படுகிறார்கள்
i) White Hat Hackers
ii) Grey Hat Hackers
iii) Black Hat Hackers
Cybersecurity in Tamil White Hat:
இங்கே White Hat Hackerஎன்பவர்கள் தங்களின் அறிவை நல்ல முறையில் பயன்படுத்துபவர்கள் இவர்கள் இணையத்தில் குற்றம் நடக்காமல் அதை தடுப்பவர்கள் மேலும் குற்றம் நடந்தாலும் அது எவ்வாறு நடந்தது என்பதை கண்டறிந்து உண்மை நிலையை எடுத்து கூறுபவர்கள் ஆவர் உதாரணத்திற்கு எங்காவது ஆன்லைனில் பணம் திருடப்பட்டால் அது எங்கே நடந்தது எவ்வாறு எந்த நாட்டிலிருந்து நடந்தது போன்றவற்றை கண்டறிந்து குற்றவாளிகளை கண்டறிய உதவுகிறார்கள்.
Grey Hat Hackers என்பவர்கள் இணையத்தில் தங்களால் ஒரு விஷத்தை செய்ய இயல்கிறதா என்று தங்களை தாங்களே சோதித்துக் கொள்ள கூடியவர்கள் இவர்கள் உண்மையில் கெட்ட நோக்கம் கொண்டவர்கள் இல்லை அவர்களால் Hacking செய்ய இயல்கிறதா என்று மட்டுமே பார்ப்பவர்கள்.
Cybersecurity in Tamil Black Hat:
மூன்றாவது நபரான Black Hat Hackers என்பவர்கள் White Hat Hackersக்கு எதிரானவர்களாகும். இவர்கள்தான் இணையத்தின் தவறான வேலைகளை செய்பவர்களாவர். இணையத்தில் நடைபெறும் அனைத்து விதமான குற்றங்களுக்கும் தகவல் திருட்டு பண திருட்டு போன்ற அனைத்திற்கும் காரணமானவர்கள் இவர்களே ஆவர்.
Malicious Program என்பதிலிருந்து திரிந்து வந்ததே Malware ஆகும் இது உங்களுக்கு தெரியாமலையே உங்கள் கணினியின் பின்னால் இயங்கி உங்களுக்கு சிக்கலை ஏற்படுத்தக் கூடியதாகும். இந்த malwareகள் அனைத்தும் Adware, Spyware என்று பல வகைப்படும் இவைகள் அனைத்தையும் தடுக்க நாம் Anti-malwareயை பயன்படுத்த வேண்டும்.
Trojan Horse என்பது ஒரு வகையான E-mailயை தாக்க கூடிய Malware ஆகும். இது Internet மூலமாக E-mail linkயை அனுப்பி பயனரின் தகவலை திருட கூடியதாகும். Phishing போன்ற திருட்டுகள் அனைத்தும் இதன் கீழ் வருபவை ஆகும். இதை முற்றிலும் தடுக்க தாங்கள் Internet Security போன்ற Antivirusகளை பயன்படுத்தலாம் உதாரணமாக Avast internet security, Kaspersky internet security போன்றவைகள்.
Password Hackingஎன்பது பயனாளரின் கடவுச்சொல்லை திருடுவதாகும் அவர்களுடைய E-mail, Facebook, Twitter மற்றும் முக்கியமாக Online Account போன்றவற்றின் கடவுச்சொல்லை திருடுவதாகும். எனவே அனைத்து விதமான கணக்குகளுக்கு ஒரே விதமான கடவுச்சொல்லை பயன்படுத்தாதீர்கள் வெவ்வேறு கடவுச்சொல்லை பயன்படுத்துங்கள் மேலும் இந்த Password Hackயை தடுக்க தற்பொழுது வங்கிகள் பண பரிவர்தனைக்கு முன்பு ஒரு OTP CODEயை நமக்கு அனுப்புகிறது இது பாதுகாப்பை கூட்டவே ஆகும். ஆகையால் தான் தற்பொழுது ஆன்லைன் கணக்கு கடவுச்சொல்லில் பல விதமான கட்டுப்பாடுகள் உள்ளன. அது ஒரு சிறிய எழுத்து, பெரிய எழுத்து, எண்கள், குறியீடுகள் போன்றவற்றின் கலவையாக இருக்க வேண்டும்.

Phishing என்பது இணைய திருடர்கள் இணையத்தில் திருட்டை அரங்கேற்றுவதற்கு கையாளும் ஒரு முறை ஆகும். இந்த பிஷிங்கில் ஹேக்கர்கள் ஒரு வலைத்தளத்தை போன்றே போலியான ஒரு வலைத்தளத்தை உருவாக்கி சம்பத்தப்பட்ட நபருக்கு எலக்ட்ரானிக் மெயில் மூலம் Linkயை அனுப்பி விடுவார்கள். சம்பந்தப்பட்ட நபரானவர் E-mailலில் குறிப்பிட்ட Linkயை திறந்து தகவல்களை உள்ளிட்டவுடன் அந்த தகவல்கள் அனைத்தும் Serverற்கு செல்லாமல் ஹேக்கரின் டேட்டாபேஸிற்கு சென்று விடும்.
DDoS Distibution denial of Service இந்த வகையான ஹேக்கர்கள் இணையத்தில் அதிகப்படியான தகவல்களை தொடர்ந்து அனுப்பி இணையத்தில் ஒரு வகையான முடக்கத்தை ஏற்படுத்துவார்கள்.
Man in the Middle இந்த வகையான ஹேக்கர்கள் நீங்கள் இணையத்தில் உங்களிடமிருந்து மற்றொரு நபருக்கு பணப்பரிவர்த்தனை செய்தால் அதை இந்த வகையான man in the middle ஹேக்கர்கள் இடையிலிருந்து திருடுகிறார்கள்.
Drive by Download இந்த வகையான மல்வாரில் நீங்கள் ஒரு வலைத்தளத்தை Browse செய்யும் போது அது தங்களுக்கே தெரியாமல் ஒரு வகையான மென்பொருளை உங்கள் கணினியில் நிறுவி தகவல்களை திருடி ஹேக்கர்களுக்கு அனுப்புகிறது.
Malvertising என்பது தாங்கள் இணையத்தை Browse செய்யும் பொழுது தென்படும் விளம்பரங்கள் மூலமாக தங்கள் கணினியில் வைரஸ் வருகிறது.
Rogue Software இதுவும் தகவல் திருட்டை ஏற்படுத்தும் மல்வார் வகையை சேர்ந்த ஒரு வகையான வைரசாகும்.
Cyber security strategy:
i) Security policy, Legal Framework
ii) Capacity building
iii) Research and Development
iv) International collabaration
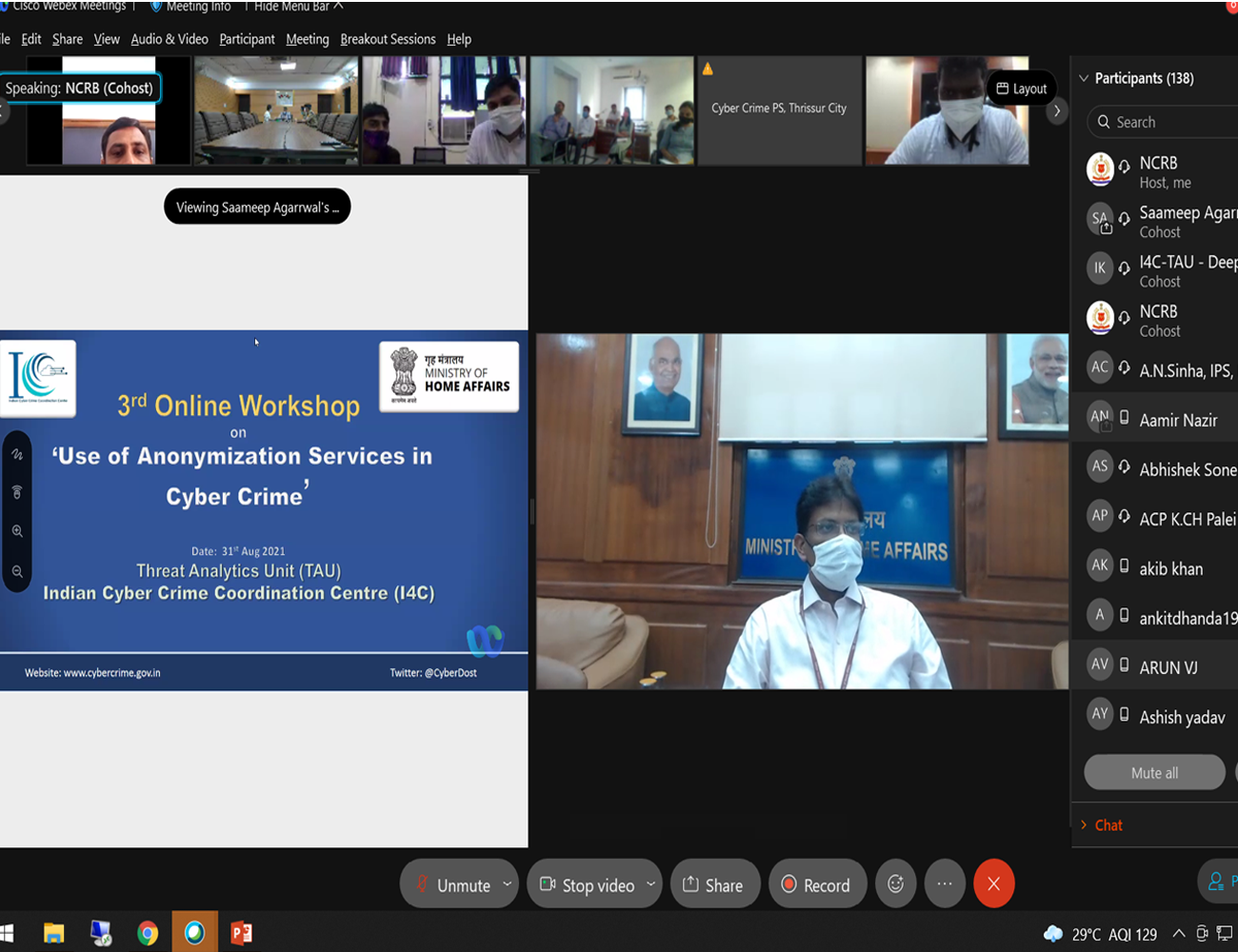
Cyber securityன் கீழ் வரக்கூடிய அனைத்து நிலைகளிலும் நிபுணர்கள் வேலை செய்து கொண்டு இருக்கிறார்கள் எவ்வாறு Cyber securityயை மேம்படுத்தி அதன் பாதுகாப்பை உறுதிபடுத்துவது என்று. உலகில் உள்ள அனைத்து நாடுகளின் Cyber security பட்டியலில் இந்தியாவானது 10வது இடத்தில் உள்ளது. 2012ம் ஆண்டு உலகின் மிகப்பெரிய 8 Cyber security attacks நடைபெற்றது.
8 Cyber security attacks in 2012:-
i) One Cyber Theft of 24 million Zappo/Amazon customers
ii) 65 Million Linkedin passwords
iii) 198 million android owners memory cards hacked
iv) 1.5 million ATM card Numbers were stolen
v) 1.5 Million eHarmony passwords were stolen
vi) Security Hole Hackers install malicious s/w on windows
vii) 27 Million user account compromised
viii) 1,656,227 computer viruses, worms,trojans attacked PC
இந்த சைபர் செக்யூரிட்டி துறையை பொறுத்தவரை தங்களுக்கு பல தரப்பான வேலை வாய்ப்புகள் கொட்டி கிடக்கிறது. இந்த வேலை வாய்ப்புகள் அனைத்தையும் கீழ்கண்ட பகுதிகளாக வகைப்படுத்தலாம்.
i) Consultancy:-
பல தரப்பட்ட Cybersecurity consultancy நிறுவனங்கள் உள்ளன. இவைகள் அனைத்தும் பல வகையான வேலைகளை செய்கின்றன. ஒரு நாளில் பல தரப்பட்ட வாடிக்கையாளர்களை சந்திக்கின்றனர். பல தரப்பட்ட துறையில் ஏற்படும் பாதுகாப்பு அச்சுறுத்தல்களை போக்குவது இவர்களின் வேலையாகும்.
Eg:- KPMG, EY, DELLOITE, PWC, AUJAS, PARAMOUNT COMPUTER SYSTEMS, MCKINSEY
ii) Security Researcher:-
அடுத்து காணப்படும் Security Researcher என்பது ஒரு குறிப்பிட்ட துறையில் மட்டுமே பணி செய்பவர்கள். உதாரணமா ஒருவர் வங்கி சம்பந்தப்பட்ட வேலை பார்த்தால் அவர்கள் அதை மட்டுமே பார்ப்பார்கள் Consultancy துறையை போல அவர்கள் மற்ற எல்ல துறைகளிலும் கால் வைக்க மாட்டார்கள். ஒரு குறிப்பிட்ட துறையில் ஏற்படும் பாதுகாப்பு அச்சுறுத்தல்களை போக்குவது இவர்களின் வேலையாகும்
Eg:- Fireeye, Mcafee, Symantec, Lakshya Labs
iii) Freelancer:-
Freelancerஎன்பது நீங்கள் நீங்களாகவே Cyber Security சம்பந்தப்பட்ட தொழில் தொடங்குவது ஆகும். இந்த வகையான Cyber Security முறையில் வேலை வாய்ப்பானது Consultancy மற்றும் Security Researcher இரண்டும் கலந்த கலவையாகும். இந்த துறையில் நீங்கள் வெற்றி பெற குறைந்த பட்சம் சில வருட அனுபவம் பெற்றிருக்க வேண்டும் மேலும் பல வித நிறுவங்களுடன் நல்ல உறவு வைத்திருப்பதும் நல்லது.
iv) Bug Bounty Hunter:-
Bug Bounty Hunter என்பது நீங்கள் பிழை கண்டறிவதாகும். ஒரு நிறுவனத்தின் பிழையை அல்லது பாதுகாப்பின்மையை அவர்களுக்கு சுட்டி காட்டுவதாகும் உதாரணத்திற்கு Facebook, Whatsapp போன்ற செயலிகளில் ஏதேனும் பாதுகாப்பு சம்பந்தமான Error இருந்தால் அதை அவர்களுக்கு சுட்டி காட்டுவதாகும். அதன் மூலமாக அவர்கள் பணம் ஈட்டுவார்கள்.
Career Growth:-
இங்கே Cyber Securityல் பணிக்கு அமர்த்தப்படும் நபர்கள் முதலில் Analyst ஆக நிறுவனத்தில் இணைகிறார்கள் பிறகு Associate Consultant, Consultant, Assistant Manager, Managerஆக மறுக்கிறார்கள் அதனை தொடர்ந்து Associate Director, Director, Executive Director, Partnerஆக பணி உயர்வு பெறுகிறார்கள்.
DON'T GIVE UP

WHAT IS CYBER CRIMES? ITS CAUSES.MEASURES TO REDUCE. / சைபர் குற்றம் என்றால் என்ன? அடிப்படை தகல்வல்களை விவரி.
[the_ad id=”2159″]
UPSC QUESTIONS
1. data security has assumed significant importance in the digitized world due to rising cyber crimes. the justice b. n. srikrishna committee report addresses issues related to data security. what, in your view, are the strengths and weakness sof the report relating to protection of personal data in cyber space 2018 paper 3, 2. cyberspace and internet : blessing or curse to the human civilization in the long run -2016 essay, 3.the cyberworld: its charms and challenges. -2000 essay.
தமிழ் ஹிந்து நாளிதழில் வெளிவந்த சைபர் குற்றங்கள் தொடர்பான அடிப்படை கேள்விகளும், அதற்கான சைபர் பாதுகாப்பு நிபுணர் சையது முகமது பதிலும்..
சைபர் குற்றம் என்றால் என்ன?, அதில் என்னென்ன வகைமைகள் இருக்கின்றன?
இணையத்தில் மேற்கொள்ளப்படும் அனைத்து குற்றச்செயல்களும் சைபர் குற்றத்துக்குள் வரும். இதில் பொதுவான சில பிரிவுகள் இருக்கின்றன. அவை
- வசைபாடல் (Trolling)
- முறைகேடாக நடத்துதல் (Abusing)
- மிரட்டுதல் (Threatening)
- பின் தொடர்தல், கண்காணித்தல் (Stalking)
- அவதூறு பரப்புதல் (Defame)
- பழிவாங்கும் எண்ணத்தில் அந்தரங்கப் படங்களை வெளியிடல் (Revenge Porn)
- மார்பிங் (Morphing)
[the_ad id=”5123″]
ட்ராலிங்கும் சைபர் குற்றத்தில் வருமா?, எந்தப் புள்ளியில் கிண்டல் குற்றமாக மாறுகிறது?
என்ன மாதிரியான ட்ரால் என்பதைப் பொறுத்து மாறும். தனி மனித கண்ணியத்தைக் குறைக்கும் வகையில் ட்ராலிங் செய்வதும் , ஆபாசமாகக் கிண்டல் செய்வதும் குற்றமே. இதற்கென தனியாகச் சட்டப்பிரிவு இல்லை. அதே நேரத்தில் ஐபிசி 1860 மற்றும் தகவல் தொழில்நுட்பச் சட்டம் 2008- ன் கீழ் இதைப் பதிவு செய்து, தண்டனை வாங்கித் தரமுடியும்.
அந்தரங்க மற்றும் நிர்வாணப் படங்களை முறைகேடாகப் பயன்படுத்துபவர்களுக்கு என்ன தண்டனை?
சைபர் குற்றங்களில் பிரதானமாக இருப்பது இதுதான். அந்தரங்கங்களை அம்பலப்படுத்துவது. இதற்கு 3 முதல் 7 ஆண்டுகள் வரை சிறை தண்டனை அளிக்க சட்டத்தில் இடமுண்டு.
இணையத்தில் கை தவறி சொடுக்கினால் ஆபாச இணையதளப் பக்கங்கள் தானாகவே கடைவிரிக்கின்றன. எப்படி இதைத் தவிர்ப்பது? அவற்றுக்குத் தடை விதிக்க தொழில்நுட்பத்தில் இடம் இருக்கிறதா?
இணையத்தின் ஆபத்துகளில் ஆபாசம் முக்கியமானது. தனிப்பட்ட வகையில் நம் இல்லக் கணினிகளில் இவற்றை 3 வழிகளில் திட்டமிட்டுத் தவிர்க்க முடியும்.
- ஒன்று பிரத்யேக செயலிகள் மூலமாக.
- இரண்டாவது விண்டோஸ் 10-ல் உள்ள பெற்றோர் வழிகாட்டி (Parental Guide),
- மூன்றாவது டிஎன்எஸ் சர்வர் வழியாக இவற்றைத் தடுக்கலாம்.
இதில் Qustodio, Net Nanny, Norton Family Premier, Kaspersky Safe Kids, FamilyTime உள்ளிட்ட செயலிகள் மூலம் நமக்குத் தேவையில்லாத வலைதளங்களை ப்ளாக் செய்துகொள்ளலாம். விண்டோஸ் 10-ல் Parental Guide-ஐ Enable செய்வதன் மூலம் வயதுக்குத் தகுந்த வகையில் குழந்தைகளோ, இளைஞர்களோ இணையத்தைப் பயன்படுத்துவதைக் கட்டுப்படுத்த முடியும்.
ஓப்பன் டிஎன்எஸ் சர்வரில் (Open DNS Server) நம்முடைய ஐபி முகவவரியைக் கொடுத்தும் தேவைப்படும் வலைதளங்களை ப்ளாக் செய்யலாம். ஆபாச வலைதளங்கள் என்றில்லை வன்முறையைத் தூண்டும் விளையாட்டுகள், மோசடி இணையதளங்கள், ஃபிஷ்ஷிங் (Phishing), சூதாட்ட தளங்கள் ஆகியவற்றையும் இவற்றின் மூலம் தடை செய்யலாம்.
தனிப்பட்ட முறையில்தான் இவற்றை நீக்க முடியுமா, அரசால் ஒட்டுமொத்த ஆபாசத் தளங்களையும் தடை செய்ய முடியாதா?
செய்யலாம். செய்திருக்கிறது. சில மாதங்களுக்கு முன்பு இந்திய அரசு அனைத்து ஆபாச தளங்களையும் தடை செய்தது. ஆனால் அவர்கள் சில நாட்களிலேயே வேறு பெயர்களில் வந்துவிட்டனர். உதாரணத்துக்கு .com என்ற பெயரில் இருக்கும் தளத்தைத் தடை செய்தால் .net என்ற பெயரில் அதே தளம் இயங்கும். இவற்றைத் தடை செய்வது ஒருமுறை மட்டுமேயான செயல்பாடாக இருக்காது. தொடர்ச்சியாக அவை உருவாகும்போதெல்லாம் அவற்றை நீக்கிக்கொண்டே இருக்கவேண்டும். அதற்கான அரசு ஆணைகள் முறையாகப் பிறப்பிக்கப்பட வேண்டும்.
கார்ப்பரேட்டுகள் அப்படித்தான் தங்களுடைய அலுவலகங்களில் ஆபாசத் தளங்களுக்கு எதிராக தொடர்ச்சியான செயல்பாட்டை மேற்கொண்டுள்ளனர்.
கலாச்சார ரீதியில் மிகவும் முற்போக்கானவர்கள் வெளிநாட்டினர். ஆடைகளிலும் குடும்பக் கட்டமைப்புகளிலும் சுதந்திர மனப்பான்மையைக் கொண்டவர்கள். இந்தியா மாதிரியான கட்டுக்கோப்பான சூழலைக் கொண்ட நாடுகளோடு ஒப்பிடும்போது அங்கே நிகழும் சைபர் குற்றங்கள் எப்படி இருக்கின்றன?
அமெரிக்கா, ரஷ்யா உள்ளிட்ட நாடுகளில், பாலியல் ரீதியான சைபர் குற்றங்கள் ஒப்பீட்டளவில் குறைவாக இருக்கின்றன. ஆனால் நிதி செயல்பாடுகள், நிறுவனங்களுக்கு எதிரான சைபர் குற்றங்கள் அதிகமாக உள்ளன.
இணையத்தில் தன்னுடைய அடையாளத்தை மறைத்து ஒருவர் தொடர்ந்து இயங்க முடியுமா?
நிச்சயமாக முடியாது. இணையத்தில் ரகசியம் என்று எதுவுமே கிடையாது. யாரும் தன்னை நிரந்தரமாக மறைத்து வாழ முடியாது. தேவைப்படும் நேரத்தில், உரிய சைபர் செக்யூரிட்டி நிபுணர்களால் எதை வேண்டுமானாலும் யாரை வேண்டுமானாலும் ட்ரேஸ் செய்யமுடியும். பல்வேறு தொழில்நுட்பங்களைப் பயன்படுத்தி குற்றவாளிகளை நிச்சயம் கண்டுபிடிக்க வேண்டும்.
பாலியல் தொந்தரவுகளை பெண்களை மட்டுமே எதிர்கொள்வதில்லை அல்லவா? ஆண்களும் இதுபோன்ற நிகழ்வுகளைச் சந்தித்திருப்பார்களே…
சைபர் குற்றங்களைப் பொறுத்தவரையில் பெண்களே முக்கிய இலக்கு. கருத்து மற்றும் மத நம்பிக்கை சார்ந்து வேண்டுமானால் ஆண்கள் தாக்கப்படுகிறார்கள். ஆனால் பாலியல் சார்ந்த தொந்தரவுகள் ஆண்களுக்கு மிக மிகக் குறைவாகவே இருக்கிறது.
எதனால் இணையக் குற்றங்கள் தொடர்ந்து அதிகரித்துக்கொண்டே இருக்கின்றன?
இணையவெளியில் மனிதர்கள் தங்களை மனிதர்களாகவே உணர்வதில்லை. நிஜ உலகத்துக்கும் சைபர் உலகத்துக்கும் நிறைய வித்தியாசங்கள் இருக்கின்றன. நிஜத்தில் கையில் பணத்தோடு செல்லும் வயதானவரை அடித்துப் போட்டுவிட்டு, பணத்தைப் பிடுங்கிச் செல்ல பெரும்பாலானோர் யோசிப்பர். சமூகம் நம்மைப் பார்த்துவிட்டால் அசிங்கமாகிவிடுமே என்று தயங்குவார்கள்.
ஆனால் இதுவே ஆன்லைனில் யாருடைய பாஸ்வேர்டாவது கிடைத்தால், அதைக் கொண்டு பணத்தைத் திருடுவது மனதை அத்தனை உறுத்துவதில்லை. ‘நமக்கு முன்னால் யாரும் இல்லை, நம்மை யாரும் பார்க்கவில்லை’ என்ற தைரியம் முதல் காரணம். ‘நாலு சுவருக்குள் நடக்கும் விஷயம்; நான்தான் இதைச் செய்தேன் என்று கண்டுபிடிக்க முடியாது’ என்ற எண்ணம் அடுத்த காரணம்.
இணையத்தின் முக்கியப் பிரச்சினையே அடையாளங்களை மறைத்துக் களமாடுவதுதான். அத்தகையோரை எப்படிக் கண்டுபிடிக்க முடியும்? அவர்களுக்கு தண்டனை வாங்கித் தரமுடியுமா?
சைபர் பிரிவில் அதற்கென உயரிய தொழில்நுட்பங்கள் இருக்கின்றன. அவற்றின் மூலம் சம்பந்தப்பட்ட நபர் வைத்திருக்கும் கணக்கு எங்கிருந்து பயன்படுத்தப்படுகிறது என்பதைக் கண்காணித்து அவர்களைக் கையும் களவுமாகப் பிடிக்கமுடியும். அவர்களுக்கு ஐபிசி 507-ன் கீழ் இரண்டு ஆண்டுகள் வரை சிறை தண்டனை அளிக்க முடியும். முறையான பெயர், முகவரி, புகைப்படம் இல்லாமல் மறைந்திருந்து குற்றச் செயல்களில் ஈடுபடுவோருக்காகவே இப்பிரிவு செயல்படுகிறது.
தன்னுடைய புகைப்படங்களோ, வீடியோக்களோ முறைகேடாக, தவறான இடங்களில் பயன்படுத்தப்பட்டது தெரிய வரும்போது பெண்கள் என்ன செய்யவேண்டும்?
முதலில் பெண்கள் இதுகுறித்து பயப்படவோ, வேதனைப்படுவதோ கூடாது. இதுபற்றிப் பேசவும் தயங்கக்கூடாது. இதுபற்றிப் பெற்றோர்களிடமோ, நண்பர்களிடமோ பேசுவது அவசியம். அடுத்ததாக சைபர் பிரிவில் புகார் கொடுக்க வேண்டும். இதன்மூலம் இரண்டு விஷயங்கள் நடக்கும். நமக்கு எதிராக நடக்கும் குற்றத்தையும் தடுக்கிறோம். குற்றவாளியைக் காட்டிக் கொடுப்பதன் மூலம் அடுத்து சமூகத்தில் நிகழவிருக்கும் குற்றங்களையும் தடுக்கிறோம்.
முதல் முறை தவறு செய்பவர்களாக இருந்தால், நம்முடைய புகாரின் மூலமாக அவர்கள் திருந்தி நல்வழிக்குத் திரும்பவும் வாய்ப்புண்டு.
சமூக ஊடகங்களையும் இணையத்தையும் தொடர்ந்து பயன்படுத்தும் பெண்களுக்கு ஏதேனும் ஆலோசனைகள் சொல்ல விரும்புகிறீர்களா?
எந்தக் காரணத்தைக் கொண்டும் உங்களுடைய அந்தரங்க நேரங்களைப் புகைப்படமாகவோ, வீடியோவாகவோ எடுக்காதீர்கள். உங்களுக்கு சங்கடத்தை ஏற்படுத்தும் வகையிலும் எந்தப் படத்தையும் எடுக்க அனுமதிக்க வேண்டாம். அது உங்களுடைய தோழராகவோ, காதலராகவோ, கணவராகவோ இருந்தாலும்கூட.
ஏனெனில் டிஜிட்டல் வடிவில் இருக்கும் எதுவுமே பாதுகாப்பானது அல்ல. இந்தக் கணத்தில் நாம் எடுக்கும் புகைப்படத்தை எந்தக் கணத்திலும் உலகமே பார்க்கமுடியும் என்பதை எப்போதும் நினைவில் கொள்ளுங்கள். மற்றவர்கள் புகைப்படங்கள் எடுக்கும்போதோ அல்லது உங்களை நீங்களே எடுத்துக்கொள்ளும்போதோ, இதில் நான் சரியாக இருக்கிறேனா என்று உங்களை நீங்களே கேட்டுக்கொள்ளுங்கள். அவ்வளவுதான்!” என்றார் சைபர் பாதுகாப்பு நிபுணர் சையது முகமது.
Cybercrimes
Cybercrimes are crimes and offenses committed against individuals, groups or businesses with a criminal motive using computers, smartphones and other modern technology. there are many types of cybercrime, such as theft (of data or resources), information warfare, phishing emails and malware attacks., types of cybercrimes, hacking: it is a simple term that defines sending illegal instruction to any other computer or network. in this case, a person’s computer is hacked so that his personal or sensitive information can be accessed. the criminal uses a variety of software to crack a person’s computer and the person may not be aware that his computer has been accessed from a remote location., child pornography and abuse: the internet is being highly used to abuse children sexually worldwide. this is also a type of cyber-crime wherein criminals solicit minors via chat rooms for the purpose of child pornography. the cybersecurity department of every nation is spending a lot of time monitoring chat rooms frequented by children with the hopes of reducing and preventing child abuse and soliciting., piracy or theft: this crime occurs when a person violates copyrights and downloads music, movies, games, and software. there are even peer sharing websites which encourage software piracy and many of these websites are now being targeted by the fbi. today, the judicial system is addressing this cybercrime and there are laws that prevent people from illegal downloading. film producers and directors often become victims of this crime., identity theft: this has become a major problem with people using the internet for cash transactions and banking services. in this cyber-crime, a criminal accesses data about a person’s bank account, credit cards, social security, debit card and other sensitive information to siphon money or to buy things online in the victim’s name. it can result in major financial losses for the victim and even spoil the victim’s credit history., malicious software: these are internet-based software or programs that are used to disrupt a network. the software is used to gain access to a system to steal sensitive information or data or causing damage to software present in the system., causes of cybercrime:, easy to access – the problem behind safeguarding a computer system from unauthorized access is that there are many possibilities of breach due to the complex technology. hackers can steal access codes, retina images, advanced voice recorders etc. that can fool biometric systems easily and bypass firewalls can be utilized to get past many security systems., capacity to store data in comparatively small space – the computer has the unique characteristic of storing data in a very small space. this makes it a lot easier for the people to steal data from any other storage and use it for own profit., complex – the computers run on operating systems and these operating systems are programmed of millions of codes. the human mind is imperfect, so they can do mistakes at any stage. the cybercriminals take advantage of these gaps., negligence – negligence is one of the characteristics of human conduct. so, there may be a possibility that protecting the computer system we may make any negligence which provides a cyber-criminal the access and control over the computer system., loss of evidence – the data related to the crime can be easily destroyed. so, loss of evidence has become a very common & obvious problem which paralyzes the system behind the investigation of cyber-crime., how to tackle cybercrime, 1.use strong passwords, 2.be social media savvy: be sure to keep your social networking profiles (facebook, twitter, youtube, etc.) are set to private. be sure to check your security settings. be careful of what information you post online. once it is on the internet it is there forever., 3.secure your mobile devices: many people are not aware that their mobile devices are also vulnerable to malicious software, such as computer viruses and hackers. be sure to download applications only from trusted sources., 4.protect your data: protect your data by using encryption for your most sensitive files such as financial records and tax returns., 5.protect your identity online: when it comes to protecting your identity online it is better to be too cautious than not cautious enough. it is critical that you be cautious when giving out personal id such as your name, address, phone number and/or financial information on the internet. be certain to make sure websites are secure when making online purchases, etc., 6.keep your computer current with the latest patches and updates: one of the best ways to keep attackers away from your computer is to apply patches and other software fixes when they become available, related posts, பெகாசஸ் (pegasus) என்றால் என்ன / what is pegasus software.
Cyber Security Essay for Students and Children
Cyber security essay.
Cybersecurity means protecting data, networks, programs and other information from unauthorized or unattended access, destruction or change. In today’s world, cybersecurity is very important because of some security threats and cyber-attacks. For data protection, many companies develop software. This software protects the data. Cybersecurity is important because not only it helps to secure information but also our system from virus attack. After the U.S.A. and China, India has the highest number of internet users.

Cyber Threats
It can be further classified into 2 types. Cybercrime – against individuals, corporates, etc.and Cyberwarfare – against a state.
Cyber Crime
Use of cyberspace, i.e. computer, internet, cellphone, other technical devices, etc., to commit a crime by an individual or organized group is called cyber-crime. Cyber attackers use numerous software and codes in cyberspace to commit cybercrime. They exploit the weaknesses in the software and hardware design through the use of malware. Hacking is a common way of piercing the defenses of protected computer systems and interfering with their functioning. Identity theft is also common.
Cybercrimes may occur directly i.e, targeting the computers directly by spreading computer viruses. Other forms include DoS attack. It is an attempt to make a machine or network resource unavailable to its intended users. It suspends services of a host connected to the internet which may be temporary or permanent.
Malware is a software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. It usually appears in the form of code, scripts, active content, and other software. ‘Malware’ refers to a variety of forms of hostile or intrusive software, for example, Trojan Horses, rootkits, worms, adware, etc.
Another way of committing cybercrime is independent of the Computer Network or Device. It includes Economic frauds. It is done to destabilize the economy of a country, attack on banking security and transaction system, extract money through fraud, acquisition of credit/debit card data, financial theft, etc.
Hinder the operations of a website or service through data alteration, data destruction. Others include using obscene content to humiliate girls and harm their reputation, Spreading pornography, threatening e-mail, assuming a fake identity, virtual impersonation. Nowadays misuse of social media in creating intolerance, instigating communal violence and inciting riots is happening a lot.
Get the huge list of more than 500 Essay Topics and Ideas
Cyber Warfare
Snowden revelations have shown that Cyberspace could become the theatre of warfare in the 21st century. Future wars will not be like traditional wars which are fought on land, water or air. when any state initiates the use of internet-based invisible force as an instrument of state policy to fight against another nation, it is called cyberwar’.
It includes hacking of vital information, important webpages, strategic controls, and intelligence. In December 2014 the cyberattack a six-month-long cyberattack on the German parliament for which the Sofacy Group is suspected. Another example 2008 cyberattack on US Military computers. Since these cyber-attacks, the issue of cyber warfare has assumed urgency in the global media.
Inexpensive Cybersecurity Measures
- The simplest thing you can do to up your security and rest easy at night knowing your data is safe is to change your passwords.
- You should use a password manager tool like LastPass, Dashlane, or Sticky Password to keep track of everything for you. These applications help you to use unique, secure passwords for every site you need while also keeping track of all of them for you.
- An easy way for an attacker to gain access to your network is to use old credentials that have fallen by the wayside. Hence delete unused accounts.
- Enabling two-factor authentication to add some extra security to your logins. An extra layer of security that makes it harder for an attacker to get into your accounts.
- Keep your Softwares up to date.
Today due to high internet penetration, cybersecurity is one of the biggest need of the world as cybersecurity threats are very dangerous to the country’s security. Not only the government but also the citizens should spread awareness among the people to always update your system and network security settings and to the use proper anti-virus so that your system and network security settings stay virus and malware-free.
Customize your course in 30 seconds
Which class are you in.

- Travelling Essay
- Picnic Essay
- Our Country Essay
- My Parents Essay
- Essay on Favourite Personality
- Essay on Memorable Day of My Life
- Essay on Knowledge is Power
- Essay on Gurpurab
- Essay on My Favourite Season
- Essay on Types of Sports
Leave a Reply Cancel reply
Your email address will not be published. Required fields are marked *
Download the App

45,000+ students realised their study abroad dream with us. Take the first step today
Meet top uk universities from the comfort of your home, here’s your new year gift, one app for all your, study abroad needs, start your journey, track your progress, grow with the community and so much more.

Verification Code
An OTP has been sent to your registered mobile no. Please verify

Thanks for your comment !
Our team will review it before it's shown to our readers.

- School Education /
✍️Essay on Cybercrime: Free Samples in 100, 200, 300 Words
- Updated on
- Apr 26, 2024
The 21st century is a digital age, where any and every task is done on the internet. All thanks to the developments in technology which have been the main factor to ease human life on earth and maybe on other plants in future. But with the benefits of technology, there are several harmful effects, one of them which has recently gained popularity; Cyber Crime.

Cybercrime has emerged as pervasive and evolved as one of the most dangerous threats to humans. There are several users on the internet who indulge in illegal and criminal activities, using computers and networks. To guide you through this hot debate topic, below we have discussed essays on cybercrime.
Table of Contents
- 1 Essay on Cybercrime in 100 Words
- 2 Essay on Cybercrime in 200 Words
- 3 Essay on Cybercrime in 300 Words
- 4 Short Essay on Cybercrime
Also Read: Essay on Student Life
Essay on Cybercrime in 100 Words
Cybercrime involves illegal activities like hacking, ransomware, cyberbullying, online fraud, etc. People who are involved in cybercrime or any similar activities are called hackers, scammers or fraudsters. Cybercrime leads to financial loss for individuals who have fallen victim to one. Cybercrime often invades a person’s privacy by stealing their personal details, including sensitive data, photos, and communication records, which can be used for blackmailing or any malicious purpose.
There are several governmental and non-government organizations which are working
To tackle cybercrime by raising awareness among the masses, cyber security training, implementing robust security protocols, and enacting comprehensive cybercrime laws.
Also Read: I Love My India Essay: 100 and 500+ Words in English for School Students
Essay on Cybercrime in 200 Words
Cybercrime is a criminal activity done online using a computer, network and internet. With the increasing use of the internet and mobile phones, the number of criminal activities has also gained pace. These criminal-minded people steal the personal details of a person, which leads to financial losses and damages the reputation of the victims. Various scams and fraudulent schemes are offered on the internet like online auctions, advance fees, or any investment scam, which are all aimed at deceiving individuals into parting with their money.
Cybercrime is not limited to financial losses or reputational damage, a more discrete term has emerged; cyberbullying. In cyberbullying, a person is harassed, humiliated, or threatened online. This can have severe psychological and emotional consequences. Ethical hackers or white hat hackers can help organizations identify vulnerabilities in their systems before malicious hackers exploit them.
Cybercrime doesn’t have any boundaries and is an international issue and international cooperation is crucial for tracking and prosecuting cybercriminals who operate across borders. To combat cybercrime effectively, a multi-faceted approach is required, involving education, technology, legislation, and international cooperation. As technology continues to advance, our efforts to combat cybercrime must keep pace to protect our increasingly interconnected world.
Also Read : Essay on Winter Season
Essay on Cybercrime in 300 Words
Economists have termed cybercrime as ‘ A Hidden Threat to the Digital World.’ Modern humans are relying on the internet for their day-to-day activities and every macro and micro activity. In this sense, the term cybercrime comes to the front. Cybercrime refers to criminal activities conducted through the use of computers, networks, and the Internet.
Cybercrime consists of various malicious activities like hacking, phishing, ransomware attacks, identity theft, online fraud, and cyberbullying. Hackers, fraudsters, scammers, criminals, and even state-sponsored actors exploit vulnerabilities in digital systems to steal sensitive information, disrupt operations, and cause financial and emotional harm to victims.
The consequences of cybercrime are far-reaching. Financial losses run into 10 digits annually, affecting individuals and organizations alike. Personal privacy is invaded as cybercriminals steal sensitive data, photos, and communication records. In cases of cyberbullying and harassment, victims suffer reputational damages, psychological distress, and emotional trauma, particularly in cases of cyberbullying and harassment.
It’s necessary to look for a multifaceted approach to deal with cybercrime, some of which are.
- Raising public awareness through campaigns where people are informed about the risks of cybercrime and educate them on best practices for online safety.
- Individuals and organizations should implement robust security protocols, regularly update software, and use multi-factor authentication to protect their digital assets.
- Governments should enact and enforce cybercrime laws, providing law enforcement agencies with the resources and expertise needed to prosecute cybercriminals effectively.
- Looking at the global nature of cybercrime, international collaboration is vital. Countries should work together to share threat intelligence and cooperate in the investigation and prosecution of cybercriminals.
- Ethical hackers can help organizations identify and rectify vulnerabilities in their systems before malicious actors exploit them.
Tackling cybercrime requires proactive measures, including education, strong cybersecurity practices, legislation, international cooperation, and the active involvement of ethical hackers.
Also Read: Essay on Green Energy PDF: 150 and 250 Words
Short Essay on Cybercrime
Find the short essay on cyber crime from below:
Cybercrime is an illegal and unethical activity which is done by hackers and fraudsters to gain financial or any other benefits for themselves.
To tackle cybercrime, several measures can be taken. Some of these measures are education and public awareness, research and innovation, ethical hacking, etc.
To write an essay on cybercrime, you need to give details on how it works and the level of danger it poses to humans. Cybercrime consists of various malicious activities like hacking, phishing, ransomware attacks, identity theft, online fraud, and cyberbullying. Hackers, fraudsters, scammers, criminals, and even state-sponsored actors exploit vulnerabilities in digital systems to steal sensitive information, disrupt operations, and cause financial and emotional harm to victims.
Related Articles
For more information about such informative articles, visit our essay writing page and make sure to follow Leverage Edu .
Shiva Tyagi
With an experience of over a year, I've developed a passion for writing blogs on wide range of topics. I am mostly inspired from topics related to social and environmental fields, where you come up with a positive outcome.
Leave a Reply Cancel reply
Save my name, email, and website in this browser for the next time I comment.
Contact no. *

Connect With Us
45,000+ students realised their study abroad dream with us. take the first step today..

Resend OTP in

Need help with?
Study abroad.
UK, Canada, US & More
IELTS, GRE, GMAT & More
Scholarship, Loans & Forex
Country Preference
New Zealand
Which English test are you planning to take?
Which academic test are you planning to take.
Not Sure yet
When are you planning to take the exam?
Already booked my exam slot
Within 2 Months
Want to learn about the test
Which Degree do you wish to pursue?
When do you want to start studying abroad.
January 2024
September 2024
What is your budget to study abroad?
How would you describe this article ?
Please rate this article
We would like to hear more.
Have something on your mind?

Make your study abroad dream a reality in January 2022 with
India's Biggest Virtual University Fair

Essex Direct Admission Day
Why attend .

Don't Miss Out

- LIVE TV NEWS18 TAMIL NEWS18 इंडिया LIVE TV NEWS18 LOKMAT
- News18 APP DOWNLOAD
- லைஃப்ஸ்டைல்
- Latest News
- டி20 உலகக்கோப்பை
- தொழில்நுட்பம்
- செங்கல்பட்டு
- கோயம்புத்தூர்
- திண்டுக்கல்
- கள்ளக்குறிச்சி
- காஞ்சிபுரம்
- கன்னியாகுமரி
- கிருஷ்ணகிரி
- மயிலாடுதுறை
- நாகப்பட்டினம்
- புதுக்கோட்டை
- ராமநாதபுரம்
- ராணிப்பேட்டை
- தூத்துக்குடி
- திருநெல்வேலி
- திருப்பத்தூர்
- திருவள்ளூர்
- திருவண்ணாமலை
- விழுப்புரம்
cyber crime
அனைத்து செய்திகளும்.

- Corpus ID: 169952675
CYBER CRIME IN TAMIL NADU AD 2000 TO AD 2009 A STUDY
- S. Haribabu
- Published 2 October 2009
- History, Law
Related Papers
Showing 1 through 3 of 0 Related Papers

Cyber-Crime News in Tamil

Cyber Crime: ``டெலிகாமில் இருந்து பேசுகிறோம்" ஆபாச வீடியோவை குறிப்பிட்டு பணம் பறிக்கும் கும்பல்..!

உஷார் மக்களே: `ஆன்லைனில் பட்டாசு வாங்கப் போறீங்களா?' - எச்சரிக்கும் Cyber Crime; காரணம் இதுதான்!

How to: சைபர் வழக்குகளை பதிவு செய்வது எப்படி? | How to register Cyber Crime?

How to: சைபர் குற்றங்களுக்கான புகாரை பதிவு செய்வது எப்படி? | How to File a Cyber Crime Complaint?

Cyber Fraud: கிரிக்கெட் வீராங்கனை பூனம் ராவத்தின் தாயாரிடம் ரூ.1 லட்சம் மோசடி! - போலீஸ் விசாரணை

`அந்த மாதிரி படம் பார்த்தால் FINE-ஆ? Govt சொல்வதென்ன?' - விளக்கும் Cyber Security Researcher | Video

ஆண்களே உஷார் - Shopping App மூலம் பணத்தை இழந்த இளைஞர்! | Cyber Security Expert Subash

Artificial Intelligence மூலம் நடக்கும் புதிய மோசடி! - அலர்ட் தரும் Cyber Security Expert

Dating Crime: டேட்டிங் ஆப் மூலம் அறிமுகமான நபர்... வீட்டுக்கு வந்தபோது நடந்த `ஷாக்' சம்பவம்.. உஷார்!

Crime: கூட்டுப் பாலியல் வன்கொடுமை; வீடியோ மிரட்டல்... உ.பி இளைஞருக்கு நேர்ந்த சோகம்!

சேலம்: மாநகர் Serious Crime Squad இன்ஸ்பெக்டர் டிஸ்மிஸ்! - உள்துறை நடவடிக்கையின் பின்னணி என்ன?

சாம்பார் கேட்டு தகராறு செய்த தந்தை, மகன்! - உணவக சூப்பர்வைஸரை அடித்தே கொன்ற சம்பவம் | Crime
- भारत सरकार Government of india
- गृह मंत्रालय Ministry of Home Affairs

राष्ट्रीय साइबर अपराध रिपोर्टिंग पोर्टल National Cyber Crime Reporting Portal

Women/Children Related Crime

FINANCIAL FRAUD

OTHER CYBER CRIME
Learning Corner
CITIZEN MANUAL
It is a document to describe the functionalities and workflow that is provided to citizens on the cybercrime portal for reporting cybercrimes.
CYBER SAFETY TIPS
To stay safe in the online world, it is important to follow important cyber safety practices which may help in protecting ourselves and our families from imminent threats that may harm our data and devices.
CYBER AWARENESS
Cyber awareness is an ongoing process of educating employees and citizens about the threats that lurk in cyberspace and how to act responsibly.
DAILY DIGEST
Comprehensive document prepared by Indian Cybercrime Coordination Centre (I4C) to aware employees and citizens about cyber fraud modus operandi.
Media Gallery
Video/Image Gallery
- Website Policies
- Privacy Policy

| Filing Complaints on National Cyber Crime Reporting Portal (NCRP)
Cyber Security Training in Tamil | தமிழில் சைபர் பாதுகாப்பு பயிற்சிLive Instructor LED Online Training Learn from Certified Experts

INR14000 INR 10000Inr 16000 inr 12000. Have Queries? Ask our Experts +91-7669 100 251 Upcoming BatchesWeekdays Regular (Class 1Hr - 1:30Hrs) / Per Session Weekend Regular (Class 3hr - 3:30Hrs) / Per Session Weekend Fasttrack (Class 4:30Hr - 5:00Hrs) / Per Session Hear it from our Graduate Can't find a batch? Pick your own scheduleRequest a Batch
Have Cracked Their Dream Job in Top MNC Companiesநிபுணர்களிடமிருந்து கற்றுக் கொள்ளுங்கள், திட்டங்களில் பயிற்சி மற்றும் ஐ.டி நிறுவனத்தில் இடம் பெறுங்கள்.
About Cyber Security Classroom And Online Training Course in TamilACTE online Training provide Cyber Security,it will educate you on how to protect computers, applications and networks from unauthorized and malicious users or software. It will cover the key cybersecurity concepts of cryptography, cyber forensics and network security in addition to topics such as mobile network security, cloud security, and ethical hacking techniques and tools. This Cybersecurity program will also address supporting concepts of information system security that are integral parts of cybersecurity. cybersecurity courses include information security, ethics, network management/analysis, programming and scripting, operating systems, and database management. Building on those foundational topics, the curriculum will also develop students' skills in the areas of risk analysis, cryptography, vulnerability testing, access control implementation, and security audit performance. Graduates of this program will be able to proactively implement sound security practices to mitigate security risks and respond quickly to security breaches and issues that may have occurred. Most Job Oriented Cyber Security Topics Covered
Is good to opting a career in Cyber Security ?
What is the scope of Cyber Security ?
Is Cyber Security will enough to create a job?Will acte help me with placements after my cyber security course completion, which language is best for cyber security.
Prerequisites to Learn Cyber Security Training?
Can a person without prior experience in programming learn Cyber Security ?
Will I Be Given Sufficient Practical Training In Cyber Security ?Is it benefit learning cyber security course.
How long does it take to skilled in Cyber Security?
 Top reasons to consider a career in Cyber Security?
Why is Cybersecurity so Important to the Healthcare Industry?Cybersecurity incorporates a number of technologies to safeguard digital data . Threats come from unauthorized access and internal missteps lead to increased risks that hackers take advantage of. Healthcare is increasingly the target of cybercriminals as bad actors learn how to successfully target unguarded or insufficiently guarded data. This includes data sharing, digital health records and medical devices that send data to hospital systems without protecting the data in transit. Health informatics makes the process more efficient. The threat of cyber attacks makes technology less reliable than it would otherwise be. At the same time, healthcare professionals rely on technology to retrieve, send and share healthcare data. Due to various cyber threats, every organization needs to invest in solutions that keep data secure without compromising access to technology for those fighting to save lives. How Has the Digital Revolution Changed Healthcare? Not too long ago, doctors had to limit their time with patients due to a mountain of complicated paperwork. The digital revolution has helped solve that problem. With fewer handwritten notes and more direct entry into electronic patient files, paperwork and the amount of time devoted to it have decreased dramatically.This is a crucial advancement as the global population soars and the number of healthcare data becomes more difficult to secure. Cybersecurity in healthcare needs to secure the network and database without slowing down the process of providing efficient care. Does Cybersecurity in Healthcare Save Money? Cybersecurity saves millions of dollars in the healthcare industry. The industry has grown rapidly in the last two decades. Now, healthcare providers deal with many more patients in an 8-hour shift than they used to in a 12-hour one. This is largely due to the reduced paper trail made possible by digital technology .With cloud-based computing, providers can share information with patients, colleagues and other departments in seconds. At the same time, safely storing and accessing patient data is also much easier. How Important Is Cybersecurity to Patients? Patients have the biggest stake in cybersecurity. After all, it’s their data and privacy that are at risk — and possibly their health. Hackers leak private information on the dark web, where it may be picked up to commit identity theft, Medicare fraud, and other crimes. Advanced cybersecurity allows medical professionals to ensure privacy and peace of mind for their patients. This also prevents legal issues related to hacked patient data. Healthcare practices are at a disadvantage due to the many endpoints in the system, including the Internet of Things (IoT) devices that feed data into the network from various endpoints. Specifically, tablets introduce vulnerability because they hold patient health records or are used to access them. No matter how much administrators shore up the network, it only takes one outdated device to open the healthcare provider up to an attack. What Improvements Need to Be Made? Healthcare organizations can take the following steps to secure their data:
Cybersecurity challenges in health care The newest cyber vulnerabilities are not necessarily an organization’s biggest cyber threat. Verizon’s 2016 Data Breach Investigations Report found that most breaches are about money and attackers usually take the easiest route to obtain the information they need. Consequently, many common threats continue to be problematic in health care, including:
Another growing threat in health care security is found in medical devices. As pacemakers and other equipment become connected to the internet, they face the same vulnerabilities as other computer systems. To ensure patient safety, the U.S. Food & Drug Administration recommended that both the manufacturer that creates the device and the health care facility that implants it take preventive security measures. Strategies for improving cybersecurity Due to the significant financial impact of data breaches in health care, health informatics and other professionals are playing an important role in ensuring that medical organizations remain secure. According to HealthIT.gov, individual health care organizations can improve their cyber security by implementing the following practices: 1. Establish a security culture : Ongoing cybersecurity training and education emphasize that every member of the organization is responsible for protecting patient data, creating a culture of security. 2. Protect mobile devices: An increasing number of health care providers are using mobile devices at work. Encryption and other protective measures are critical to ensure that any information on these devices is secure. 3. Maintain good computer habits: New employee onboarding should include training on best practices for computer use, including software and operating system maintenance. 4. Use a firewall: Anything connected to the internet should have a firewall. 5. Install and maintain anti-virus software: Simply installing anti-virus software is not enough. Continuous updates are essential for ensuring health care systems receive the best possible protection at any given time. 6. Plan for the unexpected: Files should be backed up regularly for quick and easy data restoration. Organizations should consider storing this backed-up information away from the main system if possible. 7. Control access to protected health information: Access to protected information should be granted to only those who need to view or use the data. 8. Use strong passwords and change them regularly: The Verizon report found that 63 percent of confirmed data breaches involved taking advantage of passwords that were the default, weak or stolen. Health care employees should not only use strong passwords, but ensure they are changed regularly. 9. Limit network access : Any software, applications and other additions to existing systems should not be installed by staff without prior consent from the proper organizational authorities. 10. Control physical access : Data can also be breached when physical devices are stolen. Computers and other electronics that contain protected information should be kept in locked rooms in secure areas. In addition to these recommendations, health data professionals are continually developing new strategies and best practices to ensure the safety of sensitive health data, protecting both the patient and organization from financial loss and other forms of harm. Key Features
Authorized Partners Syllabus of Cyber Security Classroom And Online Training Course in Tamil
Hands-on Real Time Cyber Security ProjectsText steganography project. This project is a secret message inside an innocent looking cover medium, stealthily, without creating any attention. Safe Folder AppThis project can manage folder by adding, deleting and renaming the folders. Our Top Hiring Partner for Placements
 Get Certified By Cyber Security & Industry Recognized ACTE Certificate Complete Your CourseGet certified, about experienced cyber security trainer.
Cyber Security Course FAQsLooking for better discount price, does acte provide placement.
Is ACTE certification good?
Work On Live Projects?
Who are the Trainers?What if i miss one (or) more class, what are the modes of training offered for this cyber security course, why should i learn cyber security course at acte.
Can I Access the Course Material in Online?What certification will i receive after course completion, how old is acte, what will be the size of a cyber security batch at acte, will i be given sufficient practical training in cyber security, how do i enroll for the cyber security course at acte.
If you want to give the Trending technology experience to your esteemed employees, we are here to help you! Group DiscountIf you have Three or more people in your training we will be delighted to offer you a group discount. 3 to 4 Peoples 5 to 9 Peoples 10+ Peoples Request for Class Room & Online Training QuotationHow & Where optgroup-Classroom Training- Chennai Velachery Anna Nagar Tambaram Porur Tnagar OMR Siruseri Adyar Thiruvanmiyur Maraimalai Nagar endoptgroup optgroup-Online Training Yes, I'm Interested in Online Training endoptgroup optgroup-Corporate Training Yes, We're Interested in Corporate Training endoptgroup Recent Interview Questions & Answers
Related Category Courses Beginner & Advanced level Classes. Hands-On Learning in Networking & Read more  Live Instructor LED Online Training Learn from Certified Experts Beginner Read more  Live Instructor LED Online Training Learn from Certified Experts 100% Read more  Beginner & Advanced level Classes. Hands-On Learning in Hardware & Read more  Trending Online Courses
Find Cyber Security Course in Other CitiesGet training quote for free, want to be our franchise. —Please choose an option— Select State (or) Union Territories Andaman and Nicobar Islands Assam Bihar Chandigarh Chhattisgarh Delhi Goa Gujarat Haryana Himachal Pradesh Jammu & Kashmir Jharkhand Karnataka Kerala Madhya Pradesh Maharashtra Manipur Meghalaya Mizoram Nagaland Odisha Puducherry Punjab Rajasthan Sikkim Tamil Nadu Telangana Tripura Uttarakhand Uttar Pradesh West Bengal Corporate Training EnquirySelect Training Courses Class Room Training Online Training Internship Training with CertificationApply to job, browse by loation, connect with course advisor, talk to a career expert, schedule 1:1 free counselling, transform your ambitions into achievements..
TestimonialsExpert-Led No.1 Executive Post Graduate Certification in Data Science & Artificial Intelligence

சைபர் கிரைம் புகார் கடிதம் எழுதுவது எப்படிCyber Crime Complaint Letter Format in Tamilதொழிநுட்பம் வளர வளர நன்மைகள் அதிகரித்து வருவது போலவே அதனுடைய தீமைகளும் வருகின்றது. சைபர் குற்றங்களை பொறுத்தவரை தற்போதைய காலகட்டத்தில் அவற்றின் எண்ணிக்கை நாளுக்கு நாள் அதிகமாகிக்கொண்டே செல்கிறது. அனுமதியில்லாமல் படங்களை பகிர்வது, ஆன்லைன் பண திருட்டு, வேலைபெற்று தருவதாக ஏமாற்றுதல் என ஆன்லைன் குற்றங்களின் எண்ணிக்கை அதிகரித்துக் கொண்டே செல்கின்றது. இதனால் நாம் பாதிக்கப்பட்டு காவல் துறையிடம் புகார் அளிக்க வேண்டுமென்றால் கடிதம் எழுதி வேண்டியிருக்கும். அதனை எப்படி எழுதுவது என்று தெரியாது. இந்த பதிவில் சைபர் கிரைம் புகார் கடிதம் எழுதுவது எப்படி என்று அறிந்து கொள்வோம் வாங்க.. சைபர் கிரைம் புகார் கடிதம்:அனுப்புநர்: தங்கள் பெயர் மற்றும் உங்கள் வயது, தகப்பனார் பெயர் தங்கள் முகவரி தொலைபேசி எண்: Related Posts
ஜூலை மாதம் 2024 அரசு விடுமுறை நாட்கள்..சம்பந்தப்பட்ட அதிகாரி, சைபர் கிரைம் பிரிவு, காவல் நிலைய முகவரி மதிப்பிற்குரிய ஐயா/மேடம், எனது பெயர் பிரகாஷ் நான் இணைய மோசடிக்கு ஆளானேன் என்பதை உங்களுக்குத் தெரிவிக்கவிக்கிறேன். 25.02.2024 அன்று, பணத்தைத் திருப்பித் தருமாறு நிறுவனத்திடமிருந்து எனக்கு செய்தி வந்தது. பணத்தைத் திரும்பப்பெறும் செய்தியில் சேர்க்கப்பட்டுள்ள URL- ஐ கிளிக் செய்யும் போது, எனது Chrome உலாவியில் பணத்தைத் திரும்பப்பெறும் படிவம் திறக்கப்பட்டது. இந்த படிவத்தை பூர்த்தி செய்து சமர்ப்பித்தேன். படிவம் சமர்ப்பித்த 2 மணி நேரத்திற்குப் பிறகு, எனது வங்கிக் கணக்கிலிருந்து ரீபண்ட் பெறுவதற்குப் பதிலாக ரூ. 5000 கழிக்கப்பட்டது. நான் நிறுவனத்தின் வாடிக்கையாளர் சேவையை தொடர்பு கொண்டேன. நிறுவனத்திலிருந்து எனக்கு அப்படி எந்த செய்தியும் அனுப்பப்படவில்லை என்று சொன்னார்கள். அந்த நேரத்தில் நான் அதிர்ச்சியடைந்தேன், நான் ஏமாற்றப்பட்டேன் என்று நம்பினேன். எனவே, தயவுசெய்து எனது கோரிக்கையை பரிசீலித்து எனக்கு தேவையானதை செய்யுமாறு கேட்டுக்கொள்கிறேன். விசாரணையின் போது உங்களுக்குத் தேவையான அனைத்து ஸ்கிரீன் ஷாட்களையும் இணைத்துள்ளேன். உண்மையுள்ள, பிரகாஷ் தொடர்பு எண் முகவரி கையொப்பம் காவல்துறை புகார் மனு எழுதுவது எப்படி நான் அனிதா பொதுநலம் வலைதளத்தில் Content Writer ஆக பணியாற்றுகிறேன். எனக்கு தொழில்நுட்பம், ஆரோக்கியம், Lifestyle, Schemes போன்றவற்றில் ஆர்வம் அதிகம் இருப்பதால் உங்களுக்கு தகவல்களை சுவாரசியமாக பதிவிடுகிறேன்.  மக்கும் குப்பை மக்காத குப்பை | Makkum Kuppai Makkatha Kuppai தொற்று நோய்களில் இருந்து நம்மை பாதுகாக்க நம்மையும் நம் சுற்றுப்புறத்தையும் தூய்மையாக வைத்திருக்க வேண்டியது...  கிறிஸ்தவம், முஸ்லீம், இந்து பண்டிகைகள் 2024..! Cultural Festivals In India..! Festivals Of Tamil Nadu 2024/ கிறிஸ்தவம், முஸ்லீம், இந்து பண்டிகைகள் 2024: வணக்கம்...  புதிய வாகனம் வாங்க நல்ல நாள் 2024..! Vehicle Purchase Muhurat 2024..! வாகனம் வாங்க ஏற்ற நாள் 2024: புதிய வாகனம் வாங்க போறீங்களா?...  விடுமுறை நாட்கள் 2024 | Government Leave Calendar 2024 in Tamil புத்தாண்டு என்றால் அனைவருக்கும் பிடிக்கும். அன்று அனைவரின் வீட்டிலும் இனிப்பு கொடுத்து புத்தாண்டு...  (ஜூலை) வளைகாப்பு செய்ய உகந்த நாள் 2024 | Seemantham Dates 2024 in Tamil..!சீமந்தம் செய்ய உகந்த மாதம்..! Good Day for Baby Shower in 2024..! Seemantham Dates: வணக்கம் தோழிகளே..! இன்றைய பதிவில் 2024-ம் ஆண்டின் கர்ப்பிணிகளுக்கு...  இன்றைய இறைச்சி விலை | சிக்கன் ரேட் டுடேகோழி கறி விலை இன்று | Chicken Indraya Vilai வணக்கம் நண்பர்களே சைவ உணவை விட அசைவ உணவுகளை விரும்பி சாப்பிடுபவர்களே உலகில் அதிகம். அதிலும்... Recent Post
 Connect On Social Media© 2024 Pothunalam.com - Pothunalam.com Owned by Weby Adroit Infotech LLP | About Us | Contact: [email protected] | Thiruvarur District -614404 Welcome Back!Login to your account below Remember Me Retrieve your passwordPlease enter your username or email address to reset your password.
Cyber Crime News in Tamil
 Cyber Crime Essay For Students Table of Contents Cyber Crime Essay: In today’s digital age, the internet has become an integral part of our lives. While it offers numerous benefits, it also brings with it a dark side – cybercrime. It is imperative for all individuals to be well-informed about the world of cybercrime, what it is, its types, and its impact. In this article, we have provided you with sample essays on cybercrime of varying lengths to help you get started on your own essay. What is Cyber Crime?Cybercrime, simply put, is criminal activity conducted online. It encompasses a wide range of illegal activities that use computers and the internet as tools to commit crimes. These crimes can be broadly categorized into four main types: financial, personal, political, and property crimes. Fill Out the Form for Expert Academic Guidance! Please indicate your interest Live Classes Books Test Series Self Learning Verify OTP Code (required) I agree to the terms and conditions and privacy policy . Fill complete details Target Exam --- Whether you need a 100-word overview or a more detailed 500-word essay on the topic “Cyber Crime Essay”, we’ve got your back. Refer to the sample essays given below.  Sample Essays on Cyber Crime100-word essay on cyber crime. Cybercrime, the dark underbelly of the digital world, is on the rise. It encompasses a range of illegal activities conducted through computers and the internet, including hacking, phishing, and online fraud. Cybercriminals exploit vulnerabilities for financial gain or personal satisfaction, causing harm to individuals and organizations. The consequences can be devastating, from financial loss to emotional distress and stolen identities. To combat cybercrime, awareness and vigilance are paramount. Adopting strong passwords, using antivirus software, and practicing safe online behavior are steps we can all take to protect ourselves in this interconnected age. Cybercrime is a threat we must confront in our digital lives. Cyber Crime Essay: 250 WordsIn today’s technology-driven world, where we rely heavily on the internet and digital devices for various aspects of our lives, the threat of cybercrime looms larger than ever. Cybercrime encompasses a wide range of illegal activities carried out in the digital realm, and its impact extends far beyond just financial losses. Hacking, a prevalent cybercrime, involves malicious individuals gaining unauthorized access to systems, risking sensitive data compromise, leading to dire consequences such as identity theft and financial ruin. Phishing scams, a common cybercrime, deceive victims into disclosing personal data, enabling criminals to commit theft and fraud with the acquired information. Online fraud is rampant in the cyber world. Criminals create fake websites or online marketplaces to dupe unsuspecting victims into making payments for goods or services that don’t exist. Victims can lose substantial sums of money in such scams. To combat cybercrime, prioritize cybersecurity by practicing safe online behavior, updating passwords, and using reliable antivirus software. Keeping software and operating systems up to date is crucial for enhanced protection. Additionally, organizations and governments need to invest in robust cybersecurity infrastructure and enact stricter regulations to deter cybercriminals. Raising awareness about the risks and consequences of cybercrime is a collective responsibility that can help safeguard our digital world. In conclusion, cybercrime is a growing menace that affects individuals, businesses, and society as a whole. Understanding the various forms of cybercrime and taking proactive steps to protect ourselves and our digital assets are essential in this interconnected age. Only through collective efforts can we hope to mitigate the ever-present threat of cybercrime.  Cyber Crime Essay: 300 WordsIn our increasingly digitized world, cybercrime has emerged as a formidable challenge. Cybercrime refers to criminal activities carried out through computer networks and the internet, encompassing a wide range of illicit actions that exploit vulnerabilities in our interconnected systems. One prevalent form of cybercrime is hacking, where individuals or groups gain unauthorized access to computer systems or networks, often with malicious intent. Hacked systems can lead to data breaches, identity theft, and financial losses for individuals and organizations alike. Phishing is another common cybercrime tactic, where scammers impersonate legitimate entities to trick individuals into revealing sensitive information, such as login credentials or credit card details. These deceptive schemes can result in severe financial and personal consequences for victims. Online fraud, including various scams and schemes, poses significant risks. It includes activities like advance-fee fraud, Ponzi schemes, and online auction fraud. Victims may suffer substantial financial losses, and recovery can be challenging. Cyberbullying and online harassment are personal cybercrimes that target individuals through hurtful, threatening, or offensive online behavior. These acts can have profound psychological and emotional effects on victims. To combat cybercrime, individuals and organizations must prioritize cybersecurity. This involves using strong, unique passwords, enabling two-factor authentication, and keeping software and antivirus programs up to date. Cybersecurity awareness and education are crucial to recognizing and avoiding potential threats. Governments and law enforcement agencies worldwide are also working to combat cybercrime by strengthening legislation and collaborating on international cybercrime investigations. However, prevention starts with individual responsibility and vigilance. In conclusion, cybercrime is an evolving threat that affects us all in the digital age. As technology advances, so do the methods employed by cybercriminals. Staying informed, practicing safe online behavior, and implementing robust cybersecurity measures are essential steps to protect ourselves and our digital assets from the growing menace of cybercrime. 500-Word Essay on Cyber Crime: In our increasingly interconnected world, where digital technology permeates every aspect of our lives, the threat of cybercrime has become a pressing concern. Cybercrime encompasses a wide range of illicit activities that occur in the digital realm, using computers, networks, and the internet as tools for criminal intent. This essay explores the evolving landscape of cybercrime, its various forms, the consequences it brings, and the measures individuals and organizations can take to combat this growing menace. The Landscape of Cybercrime Cybercrime is a multifaceted problem, constantly evolving as technology advances. It includes various forms, such as hacking, phishing, identity theft, online fraud, cyberbullying, and more. The motives behind cybercrime can be financial gain, political agenda, personal vendettas, or even thrill-seeking. Hacking is one of the most prevalent forms of cybercrime. It involves unauthorized access to computer systems, networks, or data. Hackers exploit vulnerabilities to steal sensitive information, disrupt services, or distribute malware. Phishing, on the other hand, is a deceitful practice where cybercriminals impersonate legitimate entities to trick individuals into revealing personal information or login credentials. This information is then used for malicious purposes, such as identity theft or financial fraud. Identity theft is a pervasive cybercrime, with victims experiencing devastating consequences. Cybercriminals use stolen personal information to open fraudulent accounts, apply for loans, or engage in criminal activities, often leaving the victim to deal with the legal and financial fallout. Online fraud includes various scams and schemes, such as Ponzi schemes, fake online marketplaces, and investment fraud. Victims of online fraud can lose substantial sums of money, often with little hope of recovery. The social impact of cybercrime is also significant. Cyberbullying and online harassment have become increasingly common, especially among young people. The anonymity provided by the internet allows perpetrators to engage in hurtful behavior, leading to emotional and psychological distress for the victims. The Consequences of Cybercrime The consequences of cybercrime are far-reaching and extend beyond financial losses. Individuals can experience emotional distress, anxiety, and a loss of trust in online interactions. Businesses and organizations face significant financial and reputational damage when data breaches occur. Governments grapple with the challenge of protecting national security and critical infrastructure from cyberattacks. Solutions and Prevention To combat cybercrime effectively, individuals, organizations, and governments must work together and adopt proactive measures. Here are some key steps:
The threat of cybercrime is an ever-growing challenge in our digital age. As technology advances, so do the methods and sophistication of cybercriminals. To effectively combat cybercrime, individuals, organizations, and governments must prioritize cybersecurity through awareness, education, and the implementation of robust security measures. Only by working together can we hope to mitigate the risks and consequences of cybercrime and ensure a safer digital future for all. Check Other Essays: FAQs on Cyber Crime EssayWhat is cyber crime in short essay. Cybercrime refers to criminal activities carried out using computers or the internet. Examples include online fraud, hacking, identity theft, and cyberbullying. These crimes can have serious consequences, such as financial loss, personal harm, or damage to one's reputation. To combat cybercrime, individuals must stay vigilant and follow online safety practices. What is cyber security in 100 words?Cybersecurity is the practice of safeguarding digital systems, networks, and data from a wide range of cyber threats and unauthorized access. It involves implementing measures and technologies to protect information integrity, confidentiality, and availability. Cybersecurity encompasses various aspects, including the use of strong passwords, encryption, firewalls, antivirus software, and intrusion detection systems. It is essential in today's interconnected world to mitigate the risks of data breaches, hacking, malware attacks, and other malicious activities that can lead to financial losses, reputational damage, and the compromise of personal and sensitive information. Cybersecurity is an ongoing effort to maintain the security and resilience of digital environments. Is cyber crime bad?Yes, cybercrime is bad as it can result in financial loss, emotional distress, and harm to individuals and organizations. What are the causes of cybercrime?The causes of cybercrime include technological vulnerabilities, lack of cybersecurity awareness, financial motivations, and anonymity provided by the internet. Related contentTalk to our academic expert! Language --- English Hindi Marathi Tamil Telugu Malayalam Get access to free Mock Test and Master Class Register to Get Free Mock Test and Study Material Offer Ends in 5:00 Please select class
தமிழ் அகராதி விளக்கம்
தமிழ் அகராதி
JOIN OUR NEWSLETTERSubscribe to our newsletter and stay connected வாராந்திர செய்தி மடல் பெற எங்களோடு இணைந்திருங்கள்

 To enjoy additional benefits CONNECT WITH US  Tamil Nadu cybercrime police issue advisory on deepfake scamsThe police said deepfake tech is being used by scamsters to target citizens through video calls and other means, and defraud them of money; citizens must call the cybercrime helpline if they come across any such activity. Updated - August 08, 2023 06:59 pm IST Published - August 08, 2023 05:23 pm IST - CHENNAI  Photograph used for representational purposes only | Photo Credit: Reuters The Cyber Crime Wing of the Tamil Nadu Police have issued an advisory on fake video calls that are being made by scamsters using artificial intelligence (AI) technology. Deepfake technology is being used to perpetrate several types of fraudulent scams, by creating highly convincing and realistic fake content, often using AI to manipulate audio, video, or images. Initially, this technology was primarily utilised for entertainment purposes, enabling filmmakers and content creators to seamlessly integrate actors into scenes or impersonate historical figures. However, as the technology evolved, so did its misuse by criminals seeking to exploit the power of deception, the police have said. Additional Director General of Police, Cyber Crime Wing Sanjay Kumar said, “The scam involving AI-generated deepfake video calls typically follows a series of carefully orchestrated steps, combining technological sophistication with psychological manipulation. The scamster creates a fake profile, often using stolen images or publicly-available photographs of trusted individuals, like friends or family members. They then use AI-powered deepfake technology to create highly realistic video calls on social media/other online platforms and impersonate someone the victim knows, such as a friend, family member, or colleague to deceive them into thinking it’s a genuine conversation. Later, they create a sense of urgency and request the victim to transfer money to their bank accounts.” Police said the deepfake is carefully designed to mimic the appearance and mannerisms of the impersonated person. In addition to the video manipulation, scamsters are using AI-generated voice synthesis to mimic the voice of the impersonated person, enhancing the illusion of authenticity during the video call. Mr. Kumar said, “Though there has been no complaint in this regard received so far from the State, we wish to alert citizens to be aware and to be vigilant about such frauds. People should stay informed about the latest scams, including those involving AI technology, and be cautious when receiving video calls from unexpected sources.” When receiving a video call from someone claiming to be a friend or family member, make a phone call to their personal mobile number to verify their identity before transferring any money, said the ADGP. Limit sharing of personal dataThe advisory also asks citizens to limit the amount of personal data shared online and adjust privacy settings on social media platforms to restrict access to information, and to consider using multi-factor authentication and other identity verification measures to protect accounts from unauthorised access. The Cyber Crime Wing Police also said if anyone suspects that they have been a victim of a deepfake video call fraud or have come across suspicious activity, it is crucial to take immediate action and report the incident by calling the Cyber Crime tollfree helpline number 1930 or by registering a complaint at www.cybercrime.gov.in. Citizen can also contact the concerned platform where the fraudulent activity took place, and provide them with all the relevant details, including the scamster’s profile information, messages, and any evidence collected. Related TopicsTamil Nadu / police / cyber crime Top News Today
Terms & conditions | Institutional Subscriber Comments have to be in English, and in full sentences. They cannot be abusive or personal. Please abide by our community guidelines for posting your comments. We have migrated to a new commenting platform. If you are already a registered user of The Hindu and logged in, you may continue to engage with our articles. If you do not have an account please register and login to post comments. Users can access their older comments by logging into their accounts on Vuukle. Talk to our experts 1800-120-456-456
 Essay on Cyber CrimeCyber crime is the most discussed issue of the 21st century. The technology sector world wide is witnessing a boom in the consumer of smartphones and the internet which is raising concerns with regard to the privacy and security of the users. Owing to this reason, it is highly essential for all the users to know about cyber crime & security. As a result, thi topic has become the most favorite topic of the examiner and can often be seen asked in the exams. In this view, students must have information on cyber crime and stay prepared to tackle such topics in the essay question in the English paper. IntroductionCybercrime is a dangerous attack a company or an individual may face. There are many cases where the cyber attack has brought massive loss to the company and individuals due to the data hack. We live in a technology-driven era, and every piece of information is now fed on computers. Cybercrime involves an attack on computers and digital devices. These cyber-attacks can prove hazardous not just for the organization, but also for the nation. To date, there are many digital attack cases in India and global, pushing for more security measures. These attacks are also affecting the economy of the country if not controlled in the initial stage. What is Cybercrime?Cybercrime or attack is defined as the systematic criminal activity occurring digitally and done by attackers. There are many examples of cybercrime, including fraud, malware viruses, cyberstalking and others. Due to these, government agencies and companies are investing more in the maintenance and hiring of cybercrime experts. Earlier, cybercrime was committed only by individuals or by small groups. However, now a highly complex cybercriminals network work on attacking the system for data collection. Three groups of cybercrimes- This is the form of cyberstalking, trafficking, and grooming. Over the years, this This type of cybercrime has been taken seriously by law enforcement agencies. It is now keeping a track over every such attack on an individual. Similar to the real world where criminals steal the property, in the cyber world, attackers steal data. Here, the attacker steals a person's bank details and misuse the credit card for online purchase. By using malicious software, the attacker attacks the property to disrupt the system of the organization. These types of crimes are denoted as cyber terrorism. This can be a terror because the attacker can get hold of essential documents related to government projects. An enemy nation or terrorist usually makes such attacks. There are many cases globally where a terrorist hacks government data. Apart from these, there is a financial crime where the hacker steals the money of the user account holder. Moreover, they steal company data and finance. In this type, the computer system of the person is hacked to get personal information. In many countries, including India, hacking is a punishable act. It is quite different from ethical hacking. In normal hacking, illegal use different types of software to enter the system of the target person. Hacker is then able to monitor every activity done by the person. This Cybercrime is about violating copyright and downloading music or movies. In India, many movies before their releases are leaked on the movie download sites. In other words , theft is also called privacy, which can bring a huge loss to the organization. Cyber StalkingIt is online harassment by an individual or a group of people. Normally, these stalkers target an individual and harass online. There are many cases of cyberstalking in India, resulting in the target person ending up taking Malicious SoftwareThese are computer-based cybercrimes where virus-based software is installed in the target people or organization computers. This is to damage the system and corrupt the data of the target. Laws Related to CybercrimeIn India, there are many cybercrime laws enacted to stop this threat. Be it for the individual or the organization; these laws help to either bring down the number of cases or eliminate these digital crimes. Apart from these laws, as an individual, you also need to take steps to stop these crimes. Like, not providing your login details, installing trust anti-virus software and keeping your online profile private can help to act against such Cybercrime is a significant threat that can bring huge loss to the individual and the organization. It is essential to follow basic online rules to ensure the safety of self and the organization. Benefits of Cyber Crime Essay in English provided by VedantuThe essay on cybercrime provided by Vedantu is prepared by highly qualified teachers which makes it a reliable source of information. This information could be utilized for a variety of reasons. Being a reliable piece of information the essay will benefit everyone curious to know about the topic. Following are the highlights of its benefits: Reliable information Adaptive to the context Precise language Fulfills the requirements of the students for english exam questions Comprehensive and analytical. The article digs in the depth of the issue and analyzes it through a 360 degree perspective. The essay could also be used by the students for preparing themselves for the essay question in the English paper. This essay is an excellent guide to understand what the examiner is looking for in the exam. Moreover, the topic of cybercrime is quite a recurrent one in the exam. So the students use this essay to deal with the same topic. The Essay on Cyber Crime is an excellent guide on averting any possibilities of a cyber attack. On today's date, one is mostly on the internet for a variety of reasons. It becomes essential for one to know important tips that can keep one safe from cyberbullies, thieves, or blackmailers. It is also important for one to understand the right course of actions to be taken in an eventuality of such an incident. Download the cybercrime essay for students in English on the Vedantu website.  FAQs on Cyber Crime Essay1. How Does Cybercrime Work? Group of people or an individual commits most of these cyber-crimes. These criminals use a systematic process to hack and commit these acts. These criminal communities share strategies and tools to launch attacks. Some of the cybercrime techniques Fast Flux - In this method, the hacker moves data quickly among computers in a botnet, making it challenging to find the right source. Social Engineering - This method includes using lies and manipulation to trick people into revealing their personal information. Skimmers - This involves installing a skimming tool in an ATM and stealing the information. You may find such skimming devices in ATMs. There are some digital criminals targeting organizations to steal personal information. 2. How Cybercrime Affects Society? Cybercrime can hugely affect society. In 2018, the US faced a loss of $600 billion. As consumers are increasingly allowing technologies to get into their lives, cyber attackers are getting better access. Some of the essential information available are- Personal health data, sleep schedules, and geo-locations Shopping history, account information, and passive conversations noticed voice-controlled devices, Private conversations on social media accounts. Your entire life is now available on social media, making it vulnerable to hack or cyber-attack. Attackers use different techniques including- installing malware, virus, phishing, cyberstalking, etc. These can certainly bring loss of lives and data for individuals and organizations. For society, this is a significant loss in the long run. One needs to be very careful when presenting himself socially. 3. How to stay secure in times of cybercrime? Cybercrime is a real threat posing to society. It is the 21st-century version of theft and blackmailing. There are certain ways one should adopt to prevent any possibilities of cybercrime. Do not disclose the banking details to random people or fill the CVV of your debit or credit cards on an unknown and unverified website. Keep your passwords always discrete. The camera of the laptop should always be covered. 4. Where can I get a cybercrime essay? One can find a good quality cyber crime essay on Vedantu's website. The essay which is prepared by the expert teachers describes everything that one needs to know about cybercrime. It is the one-stop solution for all your requirements on the topic. Their essay is available in PDF format on the website and could be downloaded on any device. One downloaded essay could be used in offline mode too. If one finds it feasible, the printout of the PDF could also be taken out. 
Committing cyber crimes is a mental illness. Solution in TamilMore from this Exercise The correct Answer is: 1Step by step video, text & image solution for Committing cyber crimes is a mental illness. by Physics experts to help you in doubts & scoring excellent marks in Class 10 exams. Topper's Solved these QuestionsSOCIAL HEALTH REFRACTION OF LIGHT SPACE MISSIONS Similar QuestionsWhich of following mentioned factors are important for good social health ? what is Piracy? Fill in the blanks: Laughter club is remedy to drive away……………… With a neat labelled diagram explain Rainbow Formation. Write down the formula for Maximum height. मानसिक रोग क्या है ? मानसिक रोग के कारण तथा बचाव के उपाय लिखिए । What are the steps taken by government for stopping cyber crime ? Which of the following is NOT inclded under cyber crime ? The act to curb the cyber crime. The act…………… is to curb the cyber crimes. ………….. Is the first state to start a separate cyber crime unit. Activities under the jurisdication of cyber crime laws. টীকা লেখো: মানসিক রোগ। The Act __________ is to curb the cyber crimes. ___________ is the first state to start a separate cyber crime unit. CHETAN PUBLICATION - SOCIAL HEALTH - TRU OR FALSEMeditation helps students to improve concentration in their studies. Addictive person can think rationally. Website,movies and cartoon films inappropriate for children, are banne... Children are facing problem of loneliness and menta stress dur to nucl... Brain development in adolescents is hindered due to alcoholism. Spending time with cel phones for several hours is a sort of addicitio... Radiations of cell phones penetrate the bonees of adults more effectiv... Parents threatening or hitting the children is a type of mental illne... Person indulging in selfie is aware about the world around and the ris... Banks ask our PAN/Credit card/ dibit card number on mobile phones. Committing cyber crimes is a mental illness. Yoga is limited to asanas and pranayama.  | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
IMAGES
VIDEO
COMMENTS
கணினி குற்றம் (Cyber Crime/Computer Crime) என்பது கணினியோ அல்லது வலையமைப்பு ...
i) One Cyber Theft of 24 million Zappo/Amazon customers. ii) 65 Million Linkedin passwords. iii) 198 million android owners memory cards hacked. iv) 1.5 million ATM card Numbers were stolen. v) 1.5 Million eHarmony passwords were stolen. vi) Security Hole Hackers install malicious s/w on windows.
What, in your view, are the strengths and weakness sof the Report relating to protection of personal data in cyber space? 2018 PAPER 3 2. Cyberspace and Internet : Blessing or curse to the human civilization in the long run -2016 ESSAY 3.The cyberworld: its charms and challenges. -2000 ESSAY
500+ Words Essay on Cyber Crime. Cyber Crime Essay- Everybody thinks that only stealing someone's private data is Cyber Crime. But in defining terms we can say that 'Cyber Crime refers to the use of an electronic device (computer, laptop, etc.) for stealing someone's data or trying to harm them using a computer.
Cyber Threats. It can be further classified into 2 types. Cybercrime - against individuals, corporates, etc.and Cyberwarfare - against a state. Cyber Crime. Use of cyberspace, i.e. computer, internet, cellphone, other technical devices, etc., to commit a crime by an individual or organized group is called cyber-crime.
Essay on Cybercrime in 100 Words. Cybercrime involves illegal activities like hacking, ransomware, cyberbullying, online fraud, etc. People who are involved in cybercrime or any similar activities are called hackers, scammers or fraudsters. Cybercrime leads to financial loss for individuals who have fallen victim to one.
Cyber Crime Part 1
In this video, we explained what is Cyber Crime and what are the types of cyber crime.Iot based air pollution monitoring system https://youtu.be/8rwl1W_WJ2k
4. 5. 6. Cyber Crime tamil news - Get latest and breaking tamil news about Cyber Crime, updated and published at Zee News Tamil.
மேலும் செய்திகள். Cyber Crime News in Tamil: Read Latest News on Cyber Crime along with top headlines and breaking news today in Tamil. Also get Cyber Crime latest updates, photos and videos at News18 Tamil.
Semantic Scholar extracted view of "CYBER CRIME IN TAMIL NADU AD 2000 TO AD 2009 A STUDY" by S. Haribabu. ... Search 218,874,945 papers from all fields of science. Search. Sign In Create Free Account. Corpus ID: 169952675; CYBER CRIME IN TAMIL NADU AD 2000 TO AD 2009 A STUDY
Get Latest Cyber-Crime news in Tamil: read all the breaking news headlines, top stories, videos and photos about Cyber-Crime at Vikatan
Fake mails are being sent impersonating officials of Indian Cyber Crime Coordination Centre - CEO I4C, Intelligence Bureau and Delhi Police. The claim is FAKE. Learning Corner. CITIZEN MANUAL. It is a document to describe the functionalities and workflow that is provided to citizens on the cybercrime portal for reporting cybercrimes. ...
Filing Complaints on National Cyber Crime Reporting Portal (NCRP) Report Cyber Crime Related to Women / Child. Report Anonymously. Report & Track. Report Other Cyber Crime. Report Other Cyber Crime. TAMIL NADU POLICE - CITIZEN PORTAL.
Live Instructor LED Online Training Learn from Certified Experts If you are Tamil speaker. This course will help you to learn Cyber Security in Tamil . Cyber Security becomes easy with Tamil. Beginner & Advanced level Classes. Hands-On Learning in Cyber Security. Best Practice for interview Preparation Techniques in Cyber Security. Lifetime Access for Student's […]
Cyber Crime Complaint Letter Format in Tamil. ... வரலாற்றில் இன்று ஜூன் 27 Today History in Tamil:- வரலாறு என்பது இறந்த காலத்தில் நிகழ்ந்த விஷயத்தை பற்றி நாம் தெரிந்து ...
Monday, January 8, 2024, 12:10 [IST] Latest Cyber Crime News in Tamil: Read all the breaking news headlines, top stories, videos and photos about Cyber Crime at Oneindia Tamil.
100-Word Essay on Cyber Crime. Cybercrime, the dark underbelly of the digital world, is on the rise. It encompasses a range of illegal activities conducted through computers and the internet, including hacking, phishing, and online fraud. Cybercriminals exploit vulnerabilities for financial gain or personal satisfaction, causing harm to ...
Cyber crime, இணையத்தின்வழிக் குற்றம், இணையத்தின்வழிக் குற்றம் Tamil Agaraathi ...
The Cyber Crime Wing of the Tamil Nadu Police have issued an advisory on fake video calls that are being made by scamsters using artificial intelligence (AI) technology. The police said deepfake ...
Computer Crime Act, No. 24 of 2007 1 [Certified on 09th July 2007] L. D.—O. 72/2000 AN ACT TO PROVIDE FOR THE IDENTIFICATION OF COMPUTER CRIME AND TO PROVIDE THE PROCEDURE FOR THE INVESTIGATION AND PREVENTION OF SUCH CRIMES; AND TO PROVIDE FOR MATTERS CONNECTED THEREWITH AND INCIDENTAL THERETO. BE it enacted by the Parliament of the ...
Essay on Cyber Crime. Cyber crime is the most discussed issue of the 21st century. The technology sector world wide is witnessing a boom in the consumer of smartphones and the internet which is raising concerns with regard to the privacy and security of the users. Owing to this reason, it is highly essential for all the users to know about ...
Committing cyber crimes is a mental illness. Doubtnut is No.1 Study App and Learning App with Instant Video Solutions for NCERT Class 6, Class 7, Class 8, Class 9, Class 10, Class 11 and Class 12, IIT JEE prep, NEET preparation and CBSE, UP Board, Bihar Board, Rajasthan Board, MP Board, Telangana Board etc