

a blog by Sander Berkouwer
- The things that are better left unspoken
HOWTO: Add the required Hybrid Identity URLs to the Local Intranet list of Internet Explorer and Edge

Most Microsoft-based Hybrid Identity implementations use Active Directory Federation Services (AD FS) Servers, Web Application Proxies and Azure AD Connect installations. In this series, labeled Hardening Hybrid Identity , we’re looking at hardening these implementations, using recommended practices.
In this part of the series, we’ll look at the required Hybrid Identity URLs that you want to add to the Intranet Sites list in Internet Explorer.
Note: This is the first part for adding Microsoft Cloud URLs to Internet Explorer’s zone. In this part we look at the Local Intranet zone. In the next part we look at the Trusted Sites zone.
Note: Adding URLs to the Local Intranet zone for Internet Explorer, also applies to Microsoft Edge.
Why look at the Intranet Sites?
Active Directory Federation Services (AD FS), and certain functionality in Azure Active Directory leverage Windows Integrated Authentication to allow for Single Sign-on. (SSO).
Single Sign-on reduces prompt fatigue in people and thus makes them more aware of the moments when password prompts happen and (and this is the theory…) paying more attention to what they are doing with their passwords.
I’m not a psychologist, but I do know how to make Windows Integrated Authentication work with Internet Explorer.
Intranet Sites vs. Trusted Sites (with Default settings)
Internet Explorer offers built-in zones:
- Local intranet
- Trusted sites
- Restricted sites
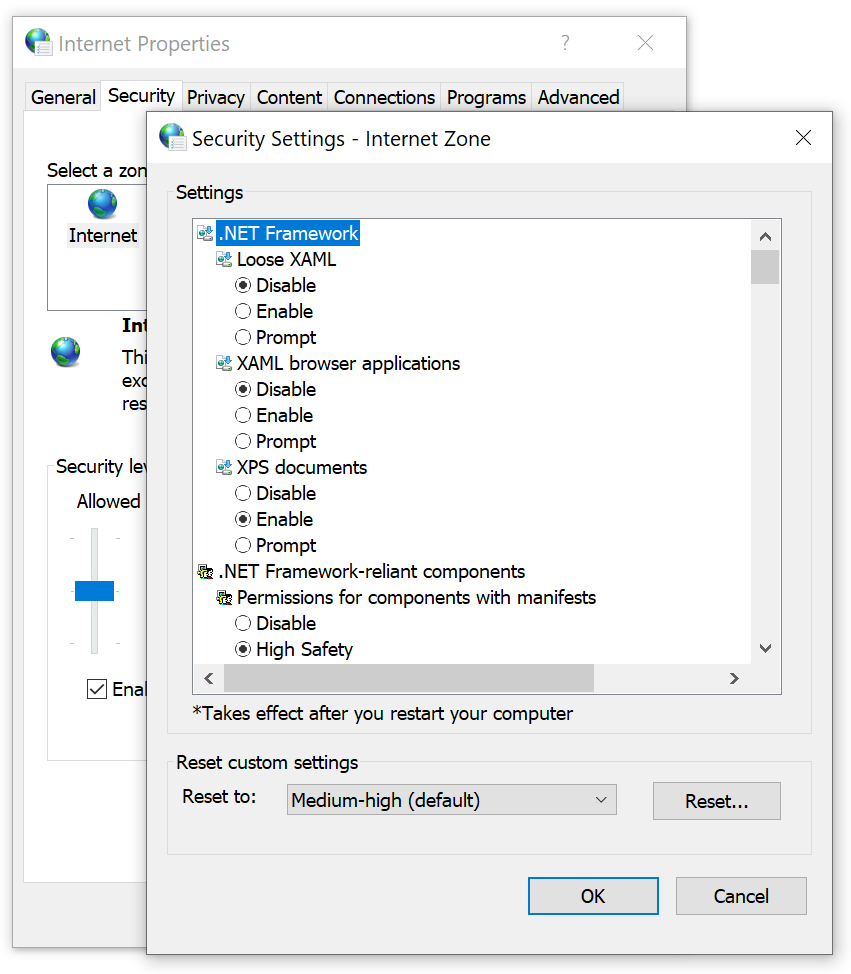
Per zone, Internet Explorer is allowed specific functionality. Restricted Sites is the most restricted zone and Internet Explorer deploys the maximum safeguards and fewer secure features (like Windows Integrated Authentication) are enabled.
The Local intranet zone, by default, offers a medium-low level of security, where Trusted sites allows for medium-level security. By default, the Local intranet zone allows for the following functionality beyond the Trusted sites zone:
- Local intranet does not allow ActiveX Filtering
- Local intranet allows Scriptlets
- Local intranet allows accessing data sources across domains (Trusted sites prompt)
- Local intranet allows scripting of Microsoft web browser control
- Sites in the Local intranet zone don’t prompt for client certificate selection when only one certificate exists
- Sites in the Local intranet zone may launch applications and unsafe files
- Sites in the Local intranet zone may navigate windows and frames across different domains
- Local intranet sites do not use the Pop-up Blocker feature
- Local intranet sites do not use the Defender SmartScreen feature
- Local intranet sites allow programmatic clipboard access
- Local intranet sites do not use the XSS Filter feature
- Local intranet sites allow user authentication
Possible negative impact (What could go wrong?)
Internet Explorer’s zones are defined with specific default settings to lower the security features for websites added to these zones.
When you use a Group Policy object to add websites that don’t need the functionality of the Local intranet zone to the zone, the systems in scope for the Group Policy object are opened up to these websites. This may result in unwanted behavior of the browser such as browser hijacks, identity theft and remote code executions.
While this does not represent a clear and immediate danger, it is a situation to avoid.
Getting ready
The best way to manage Internet Explorer zones is to use Group Policy.
To create a Group Policy object, manage settings for the Group Policy object and link it to an Organizational Unit, Active Directory site and/or Active Directory domain, log into a system with the Group Policy Management Console (GPMC) installed with an account that is either:
- A member of the Domain Admins group, or;
- The current owner of the Group Policy Object, and have the Link GPOs permission on the Organizational Unit(s), Site(s) and/or Domain(s) where the Group Policy Object is to be linked, or;
- Delegated the Edit Settings or Edit settings, delete and modify security permission on the GPO, and have the Link GPOs permission on the Organizational Unit(s), Site(s) and/or Domain(s) where the Group Policy Object is to be linked.
The URLs to add
You’ll want to add the following URLs to the Local intranet zone, depending on the way you’ve setup your Hybrid Identity implementation:
https:// <YourADFSFarmName>
When you use federation with Active Directory Federation Services (AD FS), the URL for the AD FS Farm needs to be added to the Local Intranet zone. As AD FS is authenticated against, it need to be added to the Local intranet zone as, by default, this is the only zone for websites to allow for user authentication.
https://login.microsoftonline.com
Https://secure.aadcdn.microsoftonline-p.com.
The https://login.microsoftonline.com and https://secure.aadcdn.microsoftonline-p.com URLs are the main URLs for authenticating to Microsoft cloud services. As these URLs are used to authenticate against, they need to be added to the Local intranet zone as, by default, this is the only zone for websites to allow for user authentication.
https://aadg.windows.net.nsatc.net
- https://autologon.microsoftazuread-sso.com
If you use the Seamless Single Sign-On (3SO) feature in Azure AD Connect, then you’ll want to add the following URLS to the Local intranet zone:
- https://aadg.windows.net.nsatc.net and
These URLs need to be added to the Local intranet zone on all devices where people in the organization use the 3SO feature, as these are the URLs where they will authenticate against. Trusted sites, by default, do not allow this functionality.
If you don’t use the 3SO functionality, don’t add the above URLs.
https://account.activedirectory.windowsazure.com
It is still one of Microsoft’s recommendation to add the https://account.activedirectory.windowsazure.com URL to the Local intranet zone. However, an enhanced experience is available that no longer points employees to this URL, but instead to the https://myprofile.microsoft.com URL, that uses the normal authentication URLs.
The new enhanced experience is available in the Azure portal, under User settings , Manage user feature preview settings (in the User feature previews area) named Users can use preview features for registering and managing security info – enhanced .
If you’ve enabled the enhanced preview, don’t add the above URL.
How to add the URLs to the Local Intranet zone
To add the URLs to the Local Intranet zone, perform these steps:
- Log into a system with the Group Policy Management Console (GPMC) installed.
- Open the Group Policy Management Console ( gpmc.msc )
- In the left pane, navigate to the Group Policy objects node.
- Locate the Group Policy Object that you want to use and select it, or right-click the Group Policy Objects node and select New from the menu.
- Right-click the Group Policy object and select Edit… from the menu. The Group Policy Management Editor window appears.
- In the main pane of the Group Policy Management Editor window, expand the Computer Configuration node, then Policies , Administrative Templates , Windows Components , Internet Explorer , Internet Control Panel and then the Security Page node.

- In the main pane, double-click the Sites to Zone Assignment List setting.
- Enable the Group Policy setting by selecting the Enabled option in the top pane.
- Click the Show… button in the left pane. The Show Contents window appears.

- Add the above URLs to the Local Intranet zone by entering the URL in the Value name column and the number 1 in the Value column for each of the URLs.
- Click OK when done.
- Close the Group Policy Editor window.
- In the left navigation pane of the Group Policy Management Console, navigate to the Organization Unit (OU) where you want to link the Group Policy object.
- Right-click the OU and select Link an existing GPO… from the menu.
- In the Select GPO window, select the GPO.
- Click OK to link the GPO.
Repeat the last three steps to link the GPO to all OUs that require it. Take Block Inheritance into account for OUs by linking the GPO specifically to include all people in scope.
To enable functionality in a Hybrid Identity implementation, we need to open up the web browser to allow functionality for specific web addresses. By enabling the right URLs we minimize our efforts in enabling the functionality and also minimize the negative effect on browser security.
There is no need to add all the URLs to specific Internet Explorer zones, when you don’t need to functionality. However, do not forget to add the specific URLs when you enable specific functionality like Seamless Single Sign-on and remove specific URLs when you move away from specific functionality.
Further reading
Office 365 URLs and IP address ranges Group Policy – Internet Explorer Security Zones Add Site to Local Intranet Zone Group Policy
Posted on October 15, 2019 by Sander Berkouwer in Active Directory , Entra ID , Security
5 Responses to HOWTO: Add the required Hybrid Identity URLs to the Local Intranet list of Internet Explorer and Edge

If you use the GPO methode (S2ZAL) the zone get's 'locked' so the user cannot add url's to the zone himself. If you want them to allow this ( yeah i know this shoudln't be 🙂 ) you can use a reg import with GPO Preferences instead.
Yes, indeed you can.

Very well done and written! I've only just begun writing myself just recently and realized that a lot of blogs merely rework old content but add very little of worth. It's good to see a beneficial post of some true valuue to your readers and I. It is actually going down on the list of things I need to emulate being a nnew blogger. Visitor engagement and content quality are king. Many great ideas; you've unquestionably made it on my list of sites to follow!
Continue the great work!
it's done,work fine,thanks you
Nice detail, well explained. Good work.
leave your comment cancel
This site uses Akismet to reduce spam. Learn how your comment data is processed .
Advertisement

Search this site
Dirteam.com / activedir.org blogs.
- Strategy and Stuff
- Dave Stork's IMHO
- The way I did it
- Sergio's Shack
- Things I do
- Tomek's DS World
Microsoft MVP (2009-2024)
Veeam vanguard (2016-2024), vmware vexpert (2019-2022).

Xcitium Security MVP (2023)

Recent Posts
- Four vulnerabilities in Veeam Backup Enterprise Manager were addressed in v12.1.2.172
- A Denial of Service vulnerability threatens the availability of virtual Domain Controllers on VMware ESXi (VMSA-2024-0011, Important, CVE-2024-22273)
- I’m co-presenting a session at Experts Live Netherlands 2024
- Entra's Cross-tenant Access Settings, Part 3: How to optimize end-user experiences and privacy
- Multi-Factor Authentication Server versions 8.1.15.1 and 8.1.16.1 address an AD FS Adapter installation issue
Recent Comments
- Kaper on KnowledgeBase: You experience errors with Event ID 14 and source Kerberos-Key-Distribution-Center on Domain Controllers
- Sander Berkouwer on TODO: Upgrade the Certificates for your Windows Server 2016-based Domain Controllers (and up) to enable Windows Hello for Business Hybrid Scenarios
- Alexis Belanger on TODO: Upgrade the Certificates for your Windows Server 2016-based Domain Controllers (and up) to enable Windows Hello for Business Hybrid Scenarios
- Daniel Adeniji on HOWTO: Detect NTLMv1 Authentication
- Sander Berkouwer on KnowledgeBase: App Passwords are only available to users with a non-Conditional Access MFA requirement
The information on this website is provided for informational purposes only and the authors make no warranties, either express or implied. Information in these documents, including URL and other Internet Web site references, is subject to change without notice. The entire risk of the use or the results from the use of this document remains with the user. Active Directory, Microsoft, MS-DOS, Windows, Windows NT, and Windows Server are either registered trademarks or trademarks of Microsoft Corporation in the United States and/or other countries. All other trademarks are property of their respective owners.
techlauve.com – a knowledge base for IT professionals.
Inhale problems, exhale solutions..
- Nick’s Blog
- Active Directory
- Privacy Policy
« Outlook: “Sending and Receiving reported error (OX80040600)”
Terminal Server Does Not Accept Enough Client Connections »
Adding Sites to Internet Security Zones Using Group Policy
Sometimes it is useful to leverage the power of Group Policy in Active Directory to add sites to certain security zones in Internet Explorer. This can save the network admin the trouble of managing the security zone lists for each computer (or user) separately. In the following example, each user on the network needs to have a specific site added to the Trusted Sites list.
This tutorial assumes that group policy is in good working order on the domain and that all client users and computers can access the directory.
- Open the Group Policy Management MMC console.
- Right-click the organization unit (OU) that the policy should apply to, taking special care to consider whether the policy should apply to computers or users on this particular network.
- Select “Create and Link a GPO Here…” to create a new group policy object.
- In the “New GPO” window, enter a good, descriptive name for this new policy and click “OK”. (ex. “Trusted Sites Zone – Users” or something even more descriptive)
- Locate the newly created GPO in the left-side navigation pane, right-click it and select “Edit…”
- Expand “Administrative Templates” under either “Computer Configuration” or “User Configuration” depending on which type of OU the new policy was linked to in step 2.
- The path to the settings that this example will be using is: Administrative Templates -- Windows Components -- Internet Explorer -- Internet Control Panel -- Security Page
- In the right-hand pane, double-click “Site to Zone Assignment List”.
- Enable the policy and click the “Show…” button next to “Enter the zone assignments here.” This will pop up the “Show Contents” window.
- Click the “Add…” button. This will pop up the “Add Item” window.
- In the first box, labeled “Enter the name of the item to be added:”, enter the URL to the site. (ex. https://secure.ourimportantwebapp.com) . Keep in mind that wildcards can be used. (ex. https://*.ourimportantdomain.com) . Leave off any trailing slashes or sub-folders unless that type of specific control is called for.
- 1 – Intranet Zone
- 2 – Trusted Sites Zone
- 3 – Internet Zone
- 4 – Restricted Sites Zone
- Once the zone assignment has been entered, click “OK”. This will once again show the “Show Contents” window and the new entry should be present.
- Click “OK” and “OK” again to get back to the Group Policy Management Console.
The new policy will take effect at the next group policy refresh interval, which is usually 15 minutes. To test immediately, run a gpupdate /force on a user/computer that falls into the scope of the new policy and go to “Tools -> Internet Options -> Security -> Trusted Sites -> Sites”. The site(s) added should be in the list. If the sites do not show up, check the event logs for any group policy processing errors.
Related content:
- How To: Time Sync Across Windows Network
- Group Policy Not Applied To Remote VPN Users
- QuickBooks Payroll Opens/Saves the Wrong W2 Form
- Microsoft Virtual Server Web Console Constantly Asks For Password
- Group Policy: Applying Different User Policies to the Same User for Workstations and Terminal Server
No comment yet
Juicer breville says:.
November 26, 2012 at 12:11 am (UTC -5)
Hurrah, that’s what I was looking for, what a information! existing here at this web site, thanks admin of this web page.
Leave a Reply Cancel reply
Your email address will not be published.
You may use these HTML tags and attributes: <a href="" title=""> <abbr title=""> <acronym title=""> <b> <blockquote cite=""> <cite> <code> <del datetime=""> <em> <i> <q cite=""> <s> <strike> <strong>
Submit Comment
This site uses Akismet to reduce spam. Learn how your comment data is processed .
Remember Me
Connect With Us
Connect with us.
Social Connect by NewsPress
Not finding the answer that you're looking for? Need more help with a problem that is addressed in one of our articles?
techlauve.com is affiliated with Rent-A-Nerd, Inc. in New Orleans, LA.
- DFS Replication (1)
- Group Policy (1)
- Microsoft Exhange (3)
- Microsoft Outlook (11)
- Copiers (1)
- Multi Function Devices (1)
- Printers (2)
- Scanners (1)
- Blackberry (1)
- Firewalls (2)
- Wireless (2)
- Hard Drives (1)
- SAN Systems (1)
- Hyper-V (3)
- Virtual Server (1)
- WordPress (1)
- Security (7)
- QuickBooks (2)
- Quicken (1)
- Antivirus/Antimalware (4)
- Backup Exec (2)
- Internet Explorer (5)
- Microsoft SQL (1)
- Licensing (2)
- Steinberg Nuendo (1)
- Mac OS X (1)
- Server 2003 (12)
- Server 2008 (14)
- Small Business Server 2003 (7)
- Terminal Server (6)
- Updates (2)
- Windows 7 (9)
- Windows XP (11)
- Reviews (1)
- Rent-A-Nerd, Inc.
Except where otherwise noted, content on this site is licensed under a Creative Commons Licence .
Valid XHTML 1.0 Strict Valid CSS Level 2.1
techlauve.com - a knowledge base for IT professionals. uses Graphene theme by Syahir Hakim.
- ManageEngine Products
Securing zone levels in Internet Explorer
Managing and configuring Internet Explorer can be complicated. This is especially true when users meddle with the numerous settings it houses. Users may even unknowingly enable the execution of malicious codes. This highlights the importance of securing Internet Explorer.
In this blog, we’ll talk about restricting users from changing security settings, setting trusted sites, preventing them from changing security zone policies, adding or deleting sites from security zones, and removing the Security tab altogether to ensure that users have a secure environment when using their browser.
Restricting users from changing security settings
A security zone is a list of websites at the same security level. These zones can be thought of as invisible boundaries that prevent certain web-based applications from performing unauthorized actions. These zones easily provide the appropriate level of security for the various types of web content that users are likely to encounter. Usually, sites are added or removed from a zone depending on the functionality available to users on that particular site.
To set trusted sites via GPO
- Open the Group Policy Management Editor .
- Go to User Configuration > Policies > Administrative Templates > Windows Components > Internet Explorer > Internet Control Panel > Security Page .
- Select the Site to Zone Assignment List .
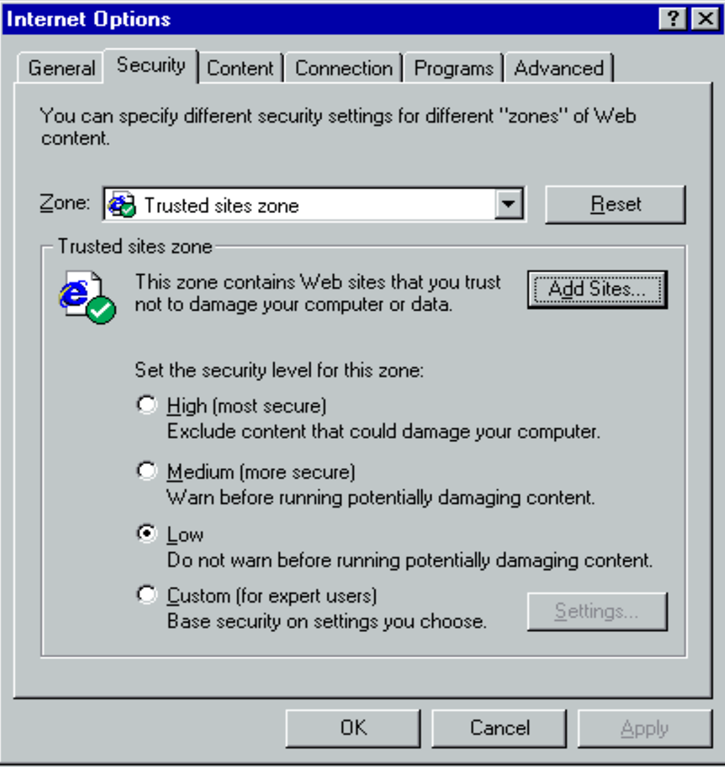
- Select Enabled and click Show to edit the list. Refer to Figure 1 below. The zone values are as follows: 1 — intranet, 2 — trusted sites, 3 — internet zone, 4 — restricted sites.
- Click Apply and OK .
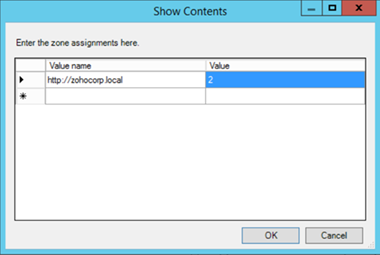
Figure 1. Assigning sites to the Trusted Sites zone.
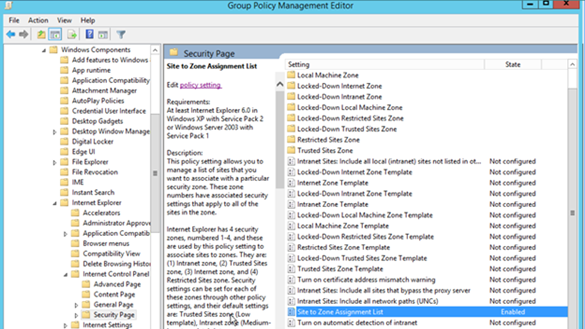
Figure 2. Enabling the Site to Zone Assignment List policy.
By enabling this policy setting, you can manage a list of sites that you want to associate with a particular security zone. See Figure 2.
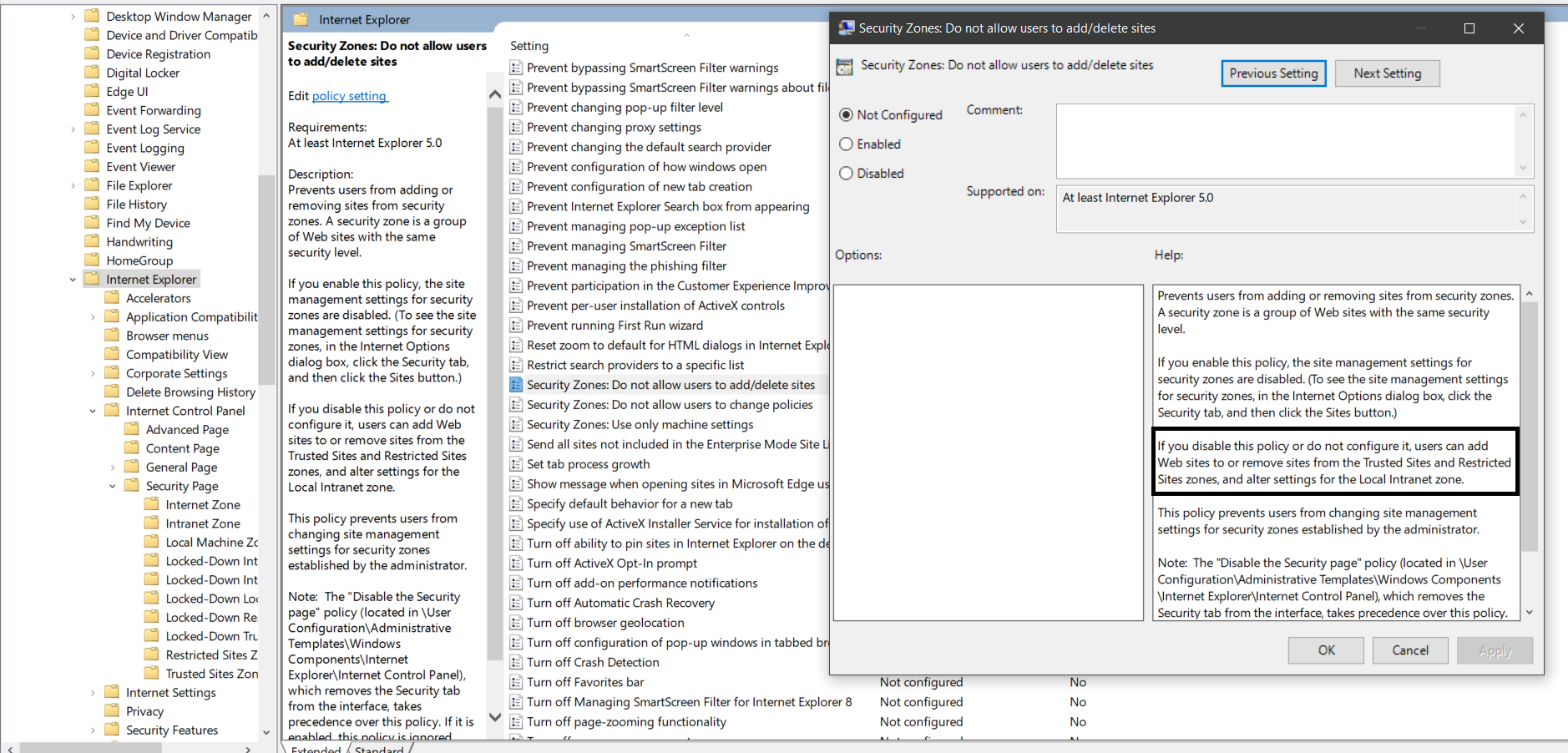
Restricting users from changing security zone policies
- Go to Computer Configuration > Administrative Templates > Windows Components > Internet Explorer .
- Double-click Security Zones: Do not allow users to change policies .
- Select Enabled .
This prevents users from changing the security zone settings set by the administrator. Once enabled, this policy disables the Custom Level button and the security-level slider on the Security tab in the Internet Options dialog box. See Figure 3.
Restricting users from adding/deleting sites from security zones
- Double-click Security Zones: Do not allow users to add/delete sites .
This disables the site management settings for security zones, and prevents users from changing site management settings for security zones established by the administrator. Users won’t be able to add or remove websites from the Trusted Sites and Restricted Sites zones or alter settings for the Local Intranet zone. See Figure 3.
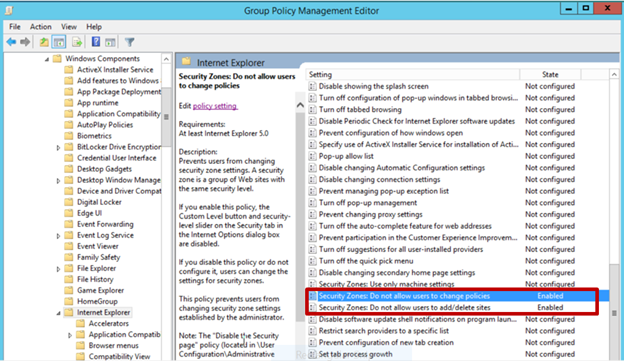
Figure 3. Enabling Security Zones: Do not allow users to change policies and Security Zones: Do not allow users to add/delete sites .
Removing the Security tab
The Security tab in Internet Explorer’s options controls access to websites by applying security settings to various download and browsing options, including defining security levels for respective security zones. By removing this tab, users will no longer be able to see or change the settings established by the administrator.
- Go to User Configuration > Policies > Administrative Templates > Windows Components > Internet Explorer > Internet Control Panel .
- Double-click Disable the Security page .
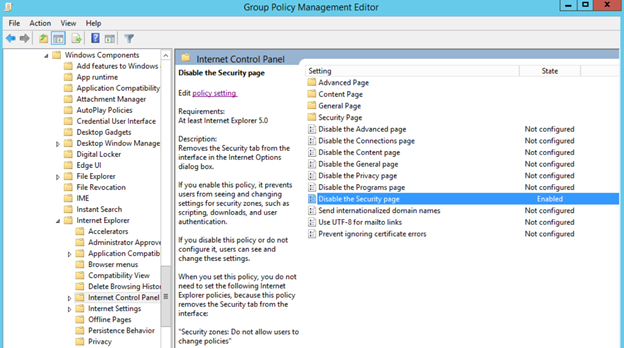
Figure 4. Enabling the Disable the Security page policy. Enabling this policy prevents users from seeing and changing settings for security zones such as scripting, downloads, and user authentication. See Figure 4.
There’s no denying the importance of securing Internet Explorer for any enterprise. By setting security levels, restricting users from changing security zone policies, preventing them from adding or deleting sites from security zones, and removing the Security tab, users will not be able to change any security settings in Microsoft Internet Explorer that have been established by the administrator. This helps you gain more control over Internet Explorer’s settings in your environment.
Derek Melber
Cancel reply.
Is there a way to enable Site to Zone assignment list and still let the user enter their own sites to the trusted list?
Hi Joe. You need to disable the below setting to achieve the requirement.
Note: Even if the policy is not configured, users can add their own sites. Only when the policy is enabled, users can’t add their own sites to trusted sites.
Thanks a lot.
Related Posts

Como fazer uma migração do Active Directory: passo a passo
Portugues 7 min read Read

Managing Internet Explorer Trusted Sites with Group Policy
Internet Explorer Maintenance is dead. We all have our regrets, missed chances, and memories. But we have to move on. Depending on your love for power, you have two options. You can take the totalitarian route (known as Administrative Templates) or the benevolent method (known as Group Policy Preferences). Here are the two ways that you can configure Internet Explorer Trusted Sites with Group Policy.
Configuring IE Trusted Sites with Administrative Templates
Site to Zone Mapping allows you to configure trusted sites with Group Policy Administrative Templates. This setting can be found at:
- Computer Configuration/Policies/Administrative Templates/Windows Components/Internet Explorer / Internet Control Panel/Security Page/Site to Zone Assignment List
- User Configuration/Policies/Administrative Templates/Windows Components/Internet Explorer / Internet Control Panel/Security Page/Site to Zone Assignment List
When possible, use the computer configuration option as it will not impact user logons. When you enable the setting, you will be prompted for a value name (the website) and a value (the zone list). Here are the possible values and the zone that they correspond to:
- 1 = Intranet/Local Zone
- 2 = Trusted Sites
- 3 = Internet/Public Zone
- 4 = Restricted Sites

The screenshot above shows one trusted site and one restricted site. There is a potential downside to managing trusted sites with Administrative Templates. You will not be able to edit the trusted sites list within Internet Explorer. If you have more than four items listed, you won’t be able to see the entire list in the IE Trusted Sites window. If you view the site properties (Alt – File – Properties), you can check a specific site’s zone though. Remember this trick as it will help you when troubleshooting! You can view the entire list in the Registry by navigating to HKLM\Software\Policies\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains. If you are an administrator, you can edit/add/remote items from this list for testing. Just be sure to run a GPUpdate /force to undo your changes.
Bonus Points : Leave a comment below explaining why a GPUpdate /force is required to undo your changes. Super Bonus Points if you answer in a haiku.
Configuring IE Trusted Sites with Group Policy Preferences Registry
You would think that Group Policy Preferences Internet Settings could set trusted sites. Unfortunately, that setting is greyed out.

You can still configure IE site mappings with Group Policy Registry Preferences though.* The benefit of this is that your users can edit the zone lists and view all of the added sites. To set this up, create a new user side registry preference. This trick will not work under computer configuration. Enter in the following details:
- Keypath: Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\WEBSITENAME
- Value Name: http
- Value Type: REG_DWORD
- Value Data: 2
Here is an example showing DeployHappiness being set as a trusted site with registry preferences:

If your site isn’t being placed in the Trusted Sites list, add it manually and then navigate to the registry location above. Ensure that the manual addition exactly matches your registry preference. You will also need to ensure that no Administrative Template Site to Zone settings are applied. If they are, they will wipe out your preference settings. Remember that Policies always win!
You can search your domain for site to zone settings by using this Group Policy Search script. Alan Burchill taught me this trick.
To see additional ways to configure site to zone mappings, read this very in depth example guide.

24 thoughts on “ Managing Internet Explorer Trusted Sites with Group Policy ”
I hope to replace our Site to Zone list to allow our users to enter their own in but I am not sure how to enter our entries that don’t specify a specific protocal such as http or https. So can someone tell me how I would create an entry for this:
*://*.sharepoint.com
and what about something like this – how would this be entered?
https://192.192.192.192 .:9443 (example only)
As for your first question, this info should help: https://community.spiceworks.com/topic/326140-add-trusted-sites-via-gpo-but-still-allow-users-to-add-trusted-sites?page=1#entry-2849140
As for the second question, I don’t know of a way to handle ports. In reference to your example, a link like that would be entered like this: *://192.192.192.192
This is excellent – I have used the GP preferences to add trused sites without locking users out of the setting if they need to add a site. But what about this – a program in the startup group – it is a shortcut to a file on a server – a member server of the local domain – domain.local. I want to prevent this program from prompting end-users to run it, and make sure it will run without prompting. Can this be accomplished with a GP preference as well? If so, do I need to add it to trusted sites, or to the local intranet zone or local machine zone? It would seem to be a local intranet or local machine zone I am working with here. I am not sure how to add it – whether I just need to add the local domain, or the computer name FQDN, or the path to the shared folder and the file. thanks!
This sounds like two different problems: 1. How do I get an app to run without prompting? 2. How do I make it run on startup with group policy?
The latter is easy, create it as a scheduled task that runs on startup. The former depends on what type of script it is. If it’s a vbscript then run it with cscript /b “name.vbs”.
With the old approach we had a file under trusted sites to allow the file to run. It has stopped working under 2012. Could I use this with a file? The old setting was:
file:\\Domain.com\netlogon\AsmallExe.exe
See this article on what you can configure with trusted sites: http://evilgpo.blogspot.com/2016/03/internet-explorer-site-to-zone.html
Just the ticket. Thanks a lot.
I have double-checked that the site to zone assignment policy is not configured, both under user and computer settings. We used group policy preferences because we do not want to lock down the trusted sites – only to push out the sites we want to be trusted. But for some absurd reason, the trusted sites are locked down and greyed out half the time – one day I will look and the sites are not dimmed out and will let me add or remove them. Then the next day they will be greyed out again. It is amazingly ridiculous. I am the only admin; no one else knows how to mess with the settings even if they had the admin credentials. So I have no clue why it keeps reverting back to the wrong settings. I thing our active directory needs to have dcdiag run on it a few times. Any ideas will be sincerely appreciated.
If it is locked down, it is a GP policy that is doing it (the site to zone assignment one) or a registry key that is enabling that site to zone assignment.
When you see one that does it, run a GPResult /h report.htm /f and look through that report.htm. You will see any GP settings that would block it then.
A reply to my own post – the problem was corrupted group policy on the Windows 7 computers – some of the computers were working fine. The ones that were not working, we had to delete the corrupt policy (it was preventing the updated policy settings from being applied). It was in the path C:\ProgramData\Microsoft\Group Policy\History\{policy GUID}. After deleting the corrupt policy and rebooting, it fixed the problem!
Thanks for the update Sam!
You’re welcome! I am still having some issues with the trusted sites being greyed out in IE, even though I made certain not to use site to zone assignment in the policy, and only used GP preferences to add registry items for the sites in the trusted zone. Do you know what registry key I need to be looking for, that might be causing this issue?
Many thanks! Sam S.
Are you making sure that you’re applying it under HKCU, and not under HKLM? If you configure it under HKCU, users will still have the ability to add their own entries. But if you configure it under HKLM, the option to add entries will be greyed out.
Yes, I definitely deployed the preferences under the Users GP Preferences and not computer policy/preferences. However, there are some policy settings that I set in both computer and user settings in the GPO. None of these are site to zone assignments though. These settings are for all the security settings within the zones, like, download signed activeX controls – enable, download unsigned activeX controls, Prompt… etc.. – these settings are set in the computer policy and the user policy which is probably what is wrong. I should probably just disable the computer policies in the GPO. I will try that and see if it helps. Why are all these settings available in the computer side and the user side both? Is there a reason someone would set these settings in one policy over the other?
A computer side policy is available for every user that logs in already. These are generally faster to apply and are my preferred way to configure something. However, times like this are when a user side policy would be the best route for you. Remove the computer side settings and try John’s suggestions. Let us know what you find out.
Sam, another thing you can try is to access the GPO from a Windows 7 workstation running IE 9 (and make sure that there are no current Internet Explorer policies being applied to the workstation; put it in an OU that is blocking inheritance if you have to), then drill down to “User Config\Policies\Windows Settings\Internet Explorer Maintenance\Security\Security Zones and Content Ratings”. Double-click on “Security Zones and Content Ratings”, then choose “Import…” under “Security Zones and Privacy’, click “Continue” when prompted, then click “Modify Settings, then “Trusted Sites”, then the “Sites” button. You can then make whatever changes you want (add a site, remove a site, remove the check from the https box, etc). This should give you the freedom you’re looking for :).
i`ve add multiple Sites to the Site to Zone assigment list (Trusted Sites). After a new logon, i`ve check my settings, start IE11, visit the site i`ve add to the list, press Alt – File – Properties and check the Zone. Some of the sites are correct, shown in the trusted site zone, some of them not, they are in an unkown zone (mixed). I want to check the registry path Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains but this key is empty, for HKLM and HKCU. What`s wrong?
Thanks and Regards Patrick
Are you deploying the trusted sites with Policies or registry preferences?
> comment below explaining why GPUpdate /force is required to undo your changes.
For Group Policy to apply efficiently changes trigger it.
Exceptions apply. GPUPDate force is one. Security too.
Less obtusely said: “Group Policy will normally only reprocess client side extensions that have at least one policy element that changed. The exceptions to this are Security Option settings which reapply every ~16 hours on most machines and every 5 minutes on Domain Controllers. The other exceptions are when you run a gpupdate /force, and any CSEs you configure to auto-reapply. You can view this decision tree by enabling UserEnv logging as described in http://technet.microsoft.com/en-us/library/cc775423%28v=ws.10%29.aspx ” … But not as haiku.
Hi, Is it possible to select the users you want that this GPO applies? It is because I need to add a web to trusted sites, but only to two users. Any idea?
You would need to configure these settings under user configuration. Then change the scope of the GPO from authenticated users to a group containing those two users.
With regards to deploying trusted sites via GPO, while allowing users to add their own entries, see if this post helps: http://community.spiceworks.com/topic/post/2849140
I’m finding that when I deploy Trusted Sites using GPP and the registry, users aren’t able to add entries themselves (it allows them to add to the list, but the entries don’t stick and are gone as soon as you reopen the dialog). Any ideas?
You sir, have a good last name! 🙂
Do you have any delete preferences configured to that registry key? If you manually browse to that key, do you see what the user added?
Leave a Reply Cancel reply
- Security Essentials
- Deploying Windows 10 (without touching a client)
- Group Policy – Preferences to Software and Everything In Between
- OneNote Can Centralize Your Documentation
- Lunch and Learn: PowerShell 3
- Lunch and Learn: Software Extraction
- Disclosure Policy
- Privacy Policy
- Rebuild the Administrative Start Menu
- Guest Posting
- What’s This? Q&A on Sponsored Posts
- Blogs that I Follow – 2018 Edition
- Books to Boost Your Career!
- Top Articles to Teach You Now!
- Top Gadgets to be more Productive!
- Software Tools
- Other – eBooks, Virtual labs, etc
- My Articles
- Clients and Desktops
- Group Policy
- Deployment/MDT
- About DeployHappiness
- February 2024
- October 2023
- January 2023
- October 2021
- November 2020
- October 2020
- February 2020
- January 2020
- November 2019
- October 2019
- February 2019
- January 2019
- December 2018
- November 2018
- October 2018
- August 2018
- February 2018
- January 2018
- December 2017
- October 2017
- September 2017
- August 2017
- February 2017
- January 2017
- October 2016
- September 2016
- August 2016
- February 2016
- January 2016
- December 2015
- October 2015
- September 2015
- August 2015
- February 2015
- January 2015
- December 2014
- November 2014
- October 2014
- September 2014
- August 2014
- February 2014
- January 2014
- December 2013
- November 2013
- October 2013
- September 2013
- August 2013
- Group Policy (85)
- Best Practice (90)
- Hardware (9)
- Management (100)
- Networking (3)
- Office 365 (8)
- Performance (23)
- Quick Tip (26)
- PowerShell (87)
- Security (28)
- Server (16)
- Thinking about IT (14)
- Training (6)
- TroubleShooting (36)
- Uncategorized (29)
- Walkthrough (109)
- Entries (RSS)
- Comments (RSS)
Stack Exchange Network
Stack Exchange network consists of 183 Q&A communities including Stack Overflow , the largest, most trusted online community for developers to learn, share their knowledge, and build their careers.
Q&A for work
Connect and share knowledge within a single location that is structured and easy to search.
Why is SiteToZoneAssignment GPO applying, but sites not appearing in IE
We have a Windows server 2012 R2 remote desktop farm, which we have applied a GPO to, to control site to zone assignments.
This was working fine up until recently, but just lately, we have found that this setting is not applying.
If I toggle ESC on, and then back off on the server I am on, the sites now show up in IE zone list for the currently logged in user. It does not however, seem to apply to all users. That list of sites will then follow them to other servers and that user will be ok moving forward.
We use user profile disks, so the users registry hive is not available on that server unless they are logged in, which might explain why it only occurs for the logged in test user.
EDIT : I can see the registry entries being created under HKCU ZoneMapKey and HKLM ZoneMap.
According to this article, IE should read settings from both of those locations, but they simply do not appear in the site list in IE control panel.
Is it possible that there has been an update for 2012 that has altered some ESC registry setting that causes us this issue?
- group-policy
- windows-server-2012-r2
- internet-explorer
- remote-desktop-services
- windows-update
- Check the zone assignment in the registry, IE ignore esc zone assignment if you have normal zone assignment. – yagmoth555 ♦ Jul 7, 2016 at 11:59
- I have applied the settings under the computer settings in the policy. If I look in HKLM\Software\Policies\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMapKey, I can see all of the entries, they just don't show up in IE itself – James Edmonds Jul 7, 2016 at 13:35
- But ESC is not enabled! – James Edmonds Jul 7, 2016 at 13:49
- I would try HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_IGNORE_POLICIES_ZONEMAP_IF_ESC_ENABLED_KB918915\ to 1 anyhow, it's for fixing a bug when ZoneMap is done and ESC is on/off. – yagmoth555 ♦ Jul 7, 2016 at 13:52
- It's tagged for Win2003, but the registry fix work in 2012; support.microsoft.com/en-gb/kb/918915 , they tell HKLM to fix it for all user, or it work too like you told in HCU – yagmoth555 ♦ Jul 7, 2016 at 14:11
3 Answers 3
I created a new user account, and when logged on for the first time, it too experienced the same issue with sites not showing in IE, even though the GPO was applied.
I found in HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap , there is a key called IEHarden (remembered the name back from my 2003 days with a similar ESC kind of issue). It looks like even though the server has ESC turned off, this key is set to 1. When either deleting, or setting this to 0, the sites immediately appear in internet control panel, and works as expected.
So while I know what is causing the problem, and have enough to fudge a workaround by deleting that key for each user on login, I still don't understand why that key is set to 1, or even exists in the first place (some users who could see the sites already, don't even have that key!). Again I can only come back to an update that has messed with IE ESC in some way.
Now have the full answer;
Two of our 8 session host created profiles with the IEHarden key, while the others did not (these two were setup by our consultants, although after asking them they are clueless).
Seems under HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Terminal Server\Install\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap the IEHarden key existed, so was being given to all new profiles created on that server.
Deleted the key from both, and all now back to normal!
Thanks James for posting the info. For anyone who faces this issue the key to look for is:
- Curious about your environment. The OPs info and references solved my related issues. But the key you're describing doesn't exist in my 2012-R2 servers. – bvj Feb 15, 2018 at 8:14
Besides IEHarden under HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap I had in my company also to set IsInstalled at HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\{A509B1A8-37EF-4b3f-8CFC-4F3A74704073} to dword:00000000 .
These two registry settings did fully resolve the issue for us. Before IEHarden was somehow set after a certain time back to 1.
You must log in to answer this question.
Not the answer you're looking for browse other questions tagged group-policy windows-server-2012-r2 internet-explorer remote-desktop-services windows-update ..
- The Overflow Blog
- An open-source development paradigm
- Developers get by with a little help from AI: Stack Overflow Knows code...
- Featured on Meta
- Testing a new version of Stack Overflow Jobs
- What deliverables would you like to see out of a working group?
Hot Network Questions
- Chicken vs Egg Symptoms from Daughter's 2005 Suburban 5.3 FlexFuel
- Is this puzzle solvable? Choose 6 five-letter words to get maximum score
- PCB layout for crystal of MSP430FR6047
- British Passport, Australian License with IDPs - Argentina to Brazil
- linkedin job post "product tester' recieved a email check PDF to deposit so I can purchase the product which I am supposed to test..Scam?
- When is the optimal time to resign before tenure?
- Preserving / fixing class imbalance
- Why is Siobhan pronounced with a /v/ sound in English?
- Is it bad style to write x^2, 2^\frac{1}{2} and 2^\sqrt{2}?
- Is there a term for 'Era when the gods walked amongst men'?
- Can unauthenticated encryption be broken if the encrypted data looks random?
- Best Latin translation of "Onwards and Upwards"
- Visibility of Planetary alignment of 6 planets on 3 June 2024 from Prague
- Windows 11 seems to have disabled all ways to get around Auto Update Restarts. Is there a workaround?
- High atmosphere combat - designing the optimal bomber
- Why Learn Measure Theory and Lebesgue Integration?
- Contemporary Fantasy w/ Magic Heroine and a Good Vampire boyfriend. Post-Buffy. Pre-Twilight
- Undecidable problems in finite graphs
- Is there a word that means both "house" and "apartment"?
- Orderings in Philosophy
- Short scary stories anthology book - Swore on a Dead Cat
- What are ordered pairs, and how does Kuratowski's definition make sense?
- Create a Windows shortcut without New > Shortcut
- A short story about two identical twins raised separately
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Internet Explorer security zones registry entries for advanced users
- 3 contributors
The retired, out-of-support Internet Explorer 11 desktop application has been permanently disabled through a Microsoft Edge update on certain versions of Windows 10. For more information, see Internet Explorer 11 desktop app retirement FAQ .
This article describes how and where Internet Explorer security zones and privacy settings are stored and managed in the registry. You can use Group Policy or the Microsoft Internet Explorer Administration Kit (IEAK) to set security zones and privacy settings.
Original product version: Internet Explorer 9, Internet Explorer 10 Original KB number: 182569
Privacy settings
Internet Explorer 6 and later versions added a Privacy tab to give users more control over cookies. This tab (select Tools , and then select Internet options ) provides flexibility for blocking or allowing cookies, based on the website that the cookie came from or the type of cookie. Types of cookies include first-party cookies, third-party cookies, and cookies that do not have a compact privacy policy. This tab also includes options to control website requests for physical location data, the ability to block pop-ups, and the ability to run toolbars and extensions when InPrivate browsing is enabled.
There are different levels of privacy on the Internet zone, and they are stored in the registry at the same location as the security zones.
You can also add a Web site to enable or to block cookies based on the Web site, regardless of the privacy policy on the Web site. Those registry keys are stored in the following registry subkey:
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Internet Settings\P3P\History
Domains that have been added as a managed site are listed under this subkey. These domains can carry either of the following DWORD values:
0x00000005 - Always Block 0x00000001 - Always Allow
Security Zone settings
For each zone, users can control how Internet Explorer handles higher-risk items such as ActiveX controls, downloads, and scripts. Internet Explorer security zones settings are stored under the following registry subkeys:
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings
- HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings
These registry keys contain the following keys:
TemplatePolicies
By default, security zones settings are stored in the HKEY_CURRENT_USER registry subtree. Because this subtree is dynamically loaded for each user, the settings for one user do not affect the settings for another.
If the Security Zones: Use only machine settings setting in Group Policy is enabled, or if the Security_HKLM_only DWORD value is present and has a value of 1 in the following registry subkey, only local computer settings are used and all users have the same security settings:
HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows\CurrentVersion\Internet Settings
With the Security_HKLM_only policy enabled, HKLM values will be used by Internet Explorer. However, the HKCU values will still be displayed in the zone settings on the Security tab in Internet Explorer. In Internet Explorer 7, the Security tab of the Internet Options dialog box displays the following message to indicate that settings are managed by the system administrator:
Some settings are managed by your system administrator If the Security Zones: Use only machine settings setting is not enabled in Group Policy, or if the Security_HKLM_only DWORD value does not exist or is set to 0 , computer settings are used together with user settings. However, only user settings appear in the Internet Options . For example, when this DWORD value does not exist or is set to 0 , HKEY_LOCAL_MACHINE settings are read together with HKEY_CURRENT_USER settings, but only HKEY_CURRENT_USER settings appear in the Internet Options .
The TemplatePolicies key determines the settings of the default security zone levels. These levels are Low, Medium Low, Medium, and High. You can change the security level settings from the default settings. However, you cannot add more security levels. The keys contain values that determine the setting for the security zone. Each key contains a Description string value and a Display Name string value that determine the text that appears on the Security tab for each security level.
The ZoneMap key contains the following keys:
- ProtocolDefaults
The Domains key contains domains and protocols that have been added to change their behavior from the default behavior. When a domain is added, a key is added to the Domains key. Subdomains appear as keys under the domain where they belong. Each key that lists a domain contains a DWORD with a value name of the affected protocol. The value of the DWORD is the same as the numeric value of the security zone where the domain is added.
The EscDomains key resembles the Domains key except that the EscDomains key applies to those protocols that are affected by the Internet Explorer Enhanced Security Configuration (IE ESC). IE ESC is introduced in Microsoft Windows Server 2003 and applies to server operating systems only.
The ProtocolDefaults key specifies the default security zone that is used for a particular protocol (ftp, http, https). To change the default setting, you can either add a protocol to a security zone by selecting Add Sites on the Security tab, or you can add a DWORD value under the Domains key. The name of the DWORD value must match the protocol name, and it must not contain any colons (:) or slashes (/).
The ProtocolDefaults key also contains DWORD values that specify the default security zones where a protocol is used. You cannot use the controls on the Security tab to change these values. This setting is used when a particular Web site does not fall in a security zone.
The Ranges key contains ranges of TCP/IP addresses. Each TCP/IP range that you specify appears in an arbitrarily named key. This key contains a :Range string value that contains the specified TCP/IP range. For each protocol, a DWORD value is added that contains the numeric value of the security zone for the specified IP range.
When the Urlmon.dll file uses the MapUrlToZone public function to resolve a particular URL to a security zone, it uses one of the following methods:
If the URL contains a fully qualified domain name (FQDN), the Domains key is processed.
In this method, an exact site match overrides a random match.
If the URL contains an IP address, the Ranges key is processed. The IP address of the URL is compared to the :Range value that is contained in the arbitrarily named keys under the Ranges key.
Because arbitrarily named keys are processed in the order that they were added to the registry, this method may find a random match before it finds a match. If this method does find a random match first, the URL may be executed in a different security zone than the zone where it is typically assigned. This behavior is by design.
The Zones key contains keys that represent each security zone that is defined for the computer. By default, the following five zones are defined (numbered zero through four):
By default, My Computer does not appear in the Zone box on the Security tab as it is locked down to help improve security.
Each of these keys contains the following DWORD values that represent corresponding settings on the custom Security tab.
Unless stated otherwise, each DWORD value is equal to zero, one, or three. Typically, a setting of zero sets a specific action as permitted, a setting of one causes a prompt to appear, and a setting of three prohibits the specific action.
Notes about 1200, 1A00, 1A10, 1E05, 1C00, and 2000
The following two registry entries affect whether you can run ActiveX controls in a particular zone:
- 1200 This registry entry affects whether you can run ActiveX controls or plug-ins.
- 2000 This registry entry controls binary behavior and script behavior for ActiveX controls or plug-ins.
Notes about 1A02, 1A03, 1A05, and 1A06
The following four registry entries take only effect if the following keys are present:
- {AEBA21FA-782A-4A90-978D-B72164C80120} First Party Cookie *
- {A8A88C49-5EB2-4990-A1A2-0876022C854F} Third-Party Cookie *
Registry entries
- 1A02 Allow persistent cookies that are stored on your computer #
- 1A03 Allow per-session cookies (not stored) #
- 1A05 Allow third party persistent cookies *
- 1A06 Allow third party session cookies *
These registry entries are located in the following registry subkey:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\<ZoneNumber>
In this registry subkey, <ZoneNumber> is a zone such as 0 (zero). The 1200 registry entry and the 2000 registry entry each contain a setting that is named Administrator approved. When this setting is enabled, the value for the particular registry entry is set to 00010000 . When the Administrator approved setting is enabled, Windows examines the following registry subkey to locate a list of approved controls:
HKEY_CURRENT_USER\Software\Policies\Microsoft\Windows\CurrentVersion\Internet Settings\AllowedControls
Logon setting (1A00) may have any one of the following values (hexadecimal):
Privacy Settings (1A10) is used by the Privacy tab slider. The DWORD values are as follows:
Block All Cookies: 00000003 High: 00000001 Medium High: 00000001 Medium: 00000001 Low: 00000001 Accept all Cookies: 00000000
Based on the settings in the slider, it will also modify the values in {A8A88C49-5EB2-4990-A1A2-0876022C854F}, {AEBA21Fa-782A-4A90-978D-B72164C80120}, or both.
The Java Permissions setting (1C00) has the following five possible values (binary):
If Custom is selected, it uses {7839DA25-F5FE-11D0-883B-0080C726DCBB} (that is located in the same registry location) to store the custom information in a binary.
Each security zone contains the Description string value and the Display Name string value. The text of these values appears on the Security tab when you select a zone in the Zone box. There is also an Icon string value that sets the icon that appears for each zone. Except for the My Computer zone, each zone contains a CurrentLevel , MinLevel , and RecommendedLevel DWORD value. The MinLevel value sets the lowest setting that can be used before you receive a warning message, CurrentLevel is the current setting for the zone, and RecommendedLevel is the recommended level for the zone.
What values for Minlevel , RecommendedLevel , and CurrentLevel mean the following:
The Flags DWORD value determines the ability of the user to modify the security zone's properties. To determine the Flags value, add the numbers of the appropriate settings together. The following Flags values are available (decimal):
If you add settings to both the HKEY_LOCAL_MACHIN E and the HKEY_CURRENT_USER subtrees, the settings are additive. If you add Web sites to both subtrees, only those Web sites in the HKEY_CURRENT_USER are visible. The Web sites in the HKEY_LOCAL_MACHINE subtree are still enforced according to their settings. However, they are not available, and you cannot modify them. This situation can be confusing because a Web site may be listed in only one security zone for each protocol.
For more information about changes to functionality in Microsoft Windows XP Service Pack 2 (SP2), visit the following Microsoft Web site:
Part 5: Enhanced Browsing Security
For more information about URL security zones, visit the following Microsoft Web site:
About URL Security Zones
For more information about how to change Internet Explorer security settings, visit the following Microsoft Web site:
Change security and privacy settings for Internet Explorer 11
For more information about Internet Explorer Local Machine Zone Lockdown, visit the following Microsoft Web site:
Internet Explorer Local Machine Zone Lockdown
For more information about values associated with the actions that can be taken in a URL security zone, see URL Action Flags .
Was this page helpful?
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback .
Submit and view feedback for
Additional resources
ericlaw talks about security, the web, and software in general
Security Zones in Edge
Last updated: 23 May 2024
Browsers As Decision Makers
As a part of every page load, browsers have to make dozens, hundreds, or even thousands of decisions — should a particular API be available? Should a resource load be permitted? Should script be allowed to run? Should video be allowed to start playing automatically? Should cookies or credentials be sent on network requests? The list is long.
In many cases, decisions are governed by two inputs: a user setting, and the URL of the page for which the decision is being made.
In the old Internet Explorer web platform, each of these decisions was called an URLAction , and the ProcessUrlAction(url, action,…) API allowed the browser or another web client to query its security manager for guidance on how to behave.

To simplify the configuration for the user or their administrator, the legacy platform classified sites into five 1 different Security Zones:
- Local Machine
- Local Intranet
Users could use the Internet Control Panel to assign specific sites to Zones and to configure the permission results for each zone. When making a decision, the browser would first map the execution context (site) to a Zone, then consult the setting for that URLAction for that Zone to decide what to do.
Reasonable defaults like “ Automatically satisfy authentication challenges from my Intranet ” meant that most users never needed to change any settings away from their defaults.
In corporate or other managed environments, administrators can use Group Policy to assign specific sites to Zones (via “Site to Zone Assignment List” policy) and specify the settings for URLActions on a per-zone basis. This allowed Microsoft IT, for instance, to configure the browser with rules like “ Treat https://mail.microsoft.com as a part of my Intranet and allow popups and file downloads without warning messages. “
Beyond manual administrative or user assignment of sites to Zones, the platform used additional heuristics that could assign sites to the Local Intranet Zone . In particular, the browser would assign dotless hostnames (e.g. https://payroll ) to the Intranet Zone, and if a Proxy Configuration script was used, any sites configured to bypass the proxy would be mapped to the Intranet Zone.
Applications hosting Web Browser Controls, by default, inherit the Windows Zone configuration settings, meaning that changes made for Internet Explorer are inherited by other applications. In relatively rare cases, the host application might supply its own Security Manager and override URL Policy decisions for embedded Web Browser Control instances.
The Trouble with Zones
While powerful and convenient, Zones are simultaneously problematic bug farms :
- Users might find that their mission critical corporate sites stopped working if their computer’s Group Policy configuration was outdated.
- Users might manually set configuration options to unsafe values without realizing it.
- Attempts to automatically provide isolation of cookies and other data by Zone led to unexpected behavior , especially for federated authentication scenarios .
Zone-mapping heuristics are extra problematic
- A Web Developer working on a site locally might find that it worked fine (Intranet Zone), but failed spectacularly for their users when deployed to production (Internet Zone).
- Users were often completely flummoxed to find that the same page on a single server behaved very differently depending on how they referred to it — e.g. http://localhost/ (Intranet Zone) vs. http://127.0.0.1/ (Internet Zone).
The fact that proxy configuration scripts can push sites into the Intranet zone proves especially challenging, because:
- A synchronous API call might need to know what Zone a caller is in, but determining that could, in the worst case, take tens of seconds — the time needed to discover the location of the proxy configuration script, download it, and run the FindProxyForUrl() function within it. This could lead to a hang and unresponsive UI.
- A site’s Zone can change at runtime without restarting the browser (say, when moving a laptop between home and work networks, or when connecting or disconnecting from a VPN).
- An IT Department might not realize the implications of returning DIRECT from a proxy configuration script and accidentally map the entire untrusted web into the highly-privileged Intranet Zone. (Microsoft IT accidentally did this circa 2011, and Google IT accidentally did it circa 2016).
- Some features like AppContainer Network Isolation are based on firewall configuration and have no inherent relationship to the browser’s Zone settings.
Legacy Edge
The legacy Edge browser (aka Spartan, Edge 18 and below) inherited the Zone architecture from its Internet Explorer predecessor with a few simplifying changes:
- Windows’ five built-in Zones were collapsed to three: Internet (Internet), the Trusted Zone (Intranet+Trusted), and the Local Computer Zone. The Restricted Zone was removed.
- Zone to URLAction mappings were hardcoded into the browser, ignoring group policies and settings in the Internet Control Panel.
Use of Zones in Chromium
Chromium goes further and favors making decisions based on explicitly-configured site lists and/or command-line arguments.
Nevertheless, in the interest of expediency, Chromium today uses Windows’ Security Zones by default in two places:
- When deciding how to handle File Downloads, and
- When deciding whether or not to release Windows Integrated Authentication (Kerberos/NTLM) credentials automatically.
For the first one, if you’ve configured the setting Launching applications and unsafe files to Disable in your Internet Control Panel’s Security tab, Chromium will block file downloads with a note: Couldn't download - Blocked .
Similarly, because Chrome uses the Windows Attachment Execute Services API to write a Mark-of-the-Web on downloaded files , the Launching applications and unsafe files setting (aka URLACTION_SHELL_EXECUTE_HIGHRISK ) for the download’s originating Zone controls whether the MoTW is written. If this setting is set to Enable (as it is for LMZ and Intranet), no MoTW is written to the file’s Zone.Identifier alternate data stream. If the Zone’s URLAction value is set to Prompt (as it is for Trusted Sites and Internet zones), the Security Zone identifier is written to the ZoneId property in the Zone.Identifier file.
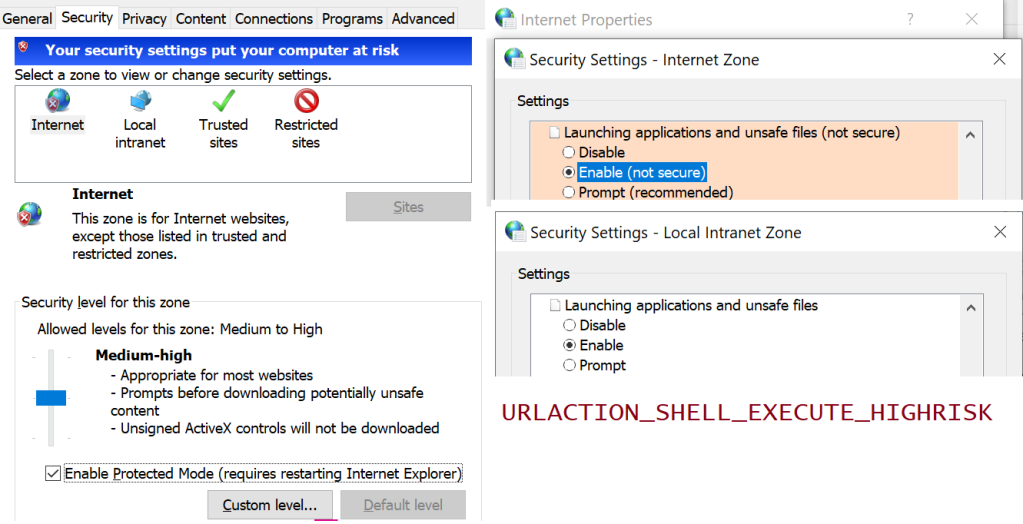
By setting a policy, Administrators can optionally configure Edge or configure Chrome to skip SmartScreen/SafeBrowsing reputation checks for File Downloads that original from the Intranet/Trusted Zone.
For the second use of Zones, Chromium will process URLACTION_CREDENTIALS_USE to decide whether Windows Integrated Authentication is used automatically, or the user should instead see a manual authentication prompt. By setting the AuthServerAllowList policy , an admin may prevent Zone Mapping from being used to decide whether credentials should be sent. Aside: the manual authentication prompt is really a bit of a mistake– the browser should instead just show a prompt: “Would you like to [Send Credentials] or [Stay Anonymous]” dialog box, rather than forcing the user to retype credentials that Windows already has.
Even Limited Use is Controversial
Any respect for Zones (or network addresses 2 ) in Chromium remains controversial— the Chrome team has launched and abandoned plans to remove all support a few times, but ultimately given up under the weight of enterprise compat concerns. The arguments for complete removal include:
- Zones are poorly documented, and Windows Zone behavior is poorly understood.
- The performance/deadlock risks mentioned earlier ( Intranet Zone mappings can come from a WPAD-discovered proxy script).
- Zones are Windows-only (meaning they prevent drop-in replacement of Windows by ChromeOS).
A sort of compromise was reached: By configuring an explicit site list policy for Windows Authentication, an administrator disables the browser’s URLACTION_CREDENTIALS_USE check, so Zones Policy is not consulted. A similar option is not presently available for Downloads.
Zones in the New Edge
Beyond the two usages of Zones inherited from upstream (Downloads and Auth), the new Chromium-based Edge browser adds three more:
- Administrators can configure Internet Explorer Mode to open all Intranet sites in IEMode . Those IEMode tabs are really running Internet Explorer, and they use Zones for everything that IE did.
- Administrators can configure Intranet Zone sites to navigate to file:// URIs which is otherwise forbidden .
- Administrators can configure Intranet Zone sites to not be put into Enhanced Security Mode .
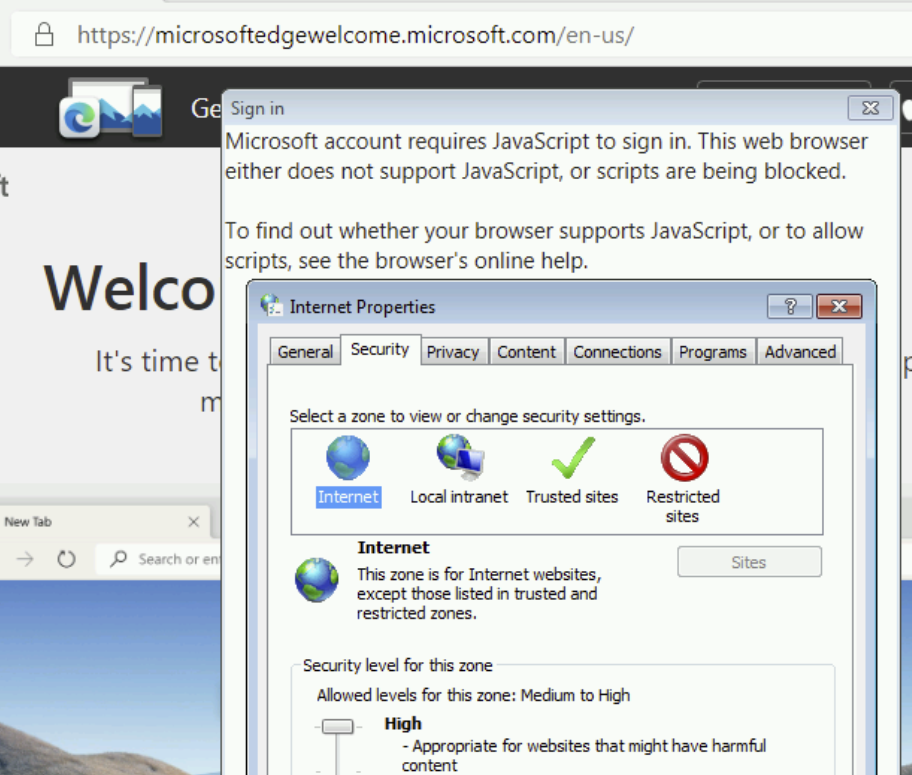
Update: This is very much a corner case, but I’ll mention it anyway. On downlevel operating systems (Windows 7/8/8.1), logging into the browser for sync makes use of a Windows dialog box that contains a Web Browser Control (based on MSHTML) that loads the login page. If you adjust your Windows Security Zones settings to block JavaScript from running in the Internet Zone, you will find that you’re unable to log into the new browser .
Downsides/Limitations
While it’s somewhat liberating that we’ve moved away from the bug farm of Security Zones, it also gives us one less tool to make things convenient or compatible for our users and IT admins.
We’ve already heard from some customers that they’d like to have a different security and privacy posture for sites on their “Intranet”, with behaviors like:
- Disable the Tracking Prevention , “Block 3rd party cookie”, and other privacy-related controls for the Intranet (like IE/Edge did).
- Allow navigation to file:// URIs from the Intranet like IE/Edge did (policy was added to Edge 95).
- Disable “ HTTP and mixed content are unsafe ” and “ TLS/1.0 and TLS/1.1 are deprecated ” nags. ( Update: Now pretty obsolete as these no longer exist )
- Skip SmartScreen website checks for the Trusted/Intranet zones ( available for Download checks only).
- Allow ClickOnce/DirectInvoke / Auto-opening Downloads from the Intranet without a prompt. Previously, Edge (Spartan)/IE respected the FTA_OpenIsSafe bit in the EditFlags for the application.manifest progid if-and-only-if the download source was in the Intranet/Trusted Sites Zone. As of Edge 94, other policies can be used.
- Allow launching application protocols from the Intranet without a prompt .
- Drop all Referrers when navigating from the Intranet to the Internet; leave Referrers alone when browsing the Intranet. (Update: less relevant now ).
- Internet Explorer and legacy Edge automatically send your client certificate to Intranet sites that ask for it. The AutoSelectCertificateForUrls policy permits Edge to send a client certificate to specified sites without a prompt, but this policy requires the administrator to manually specify the site list.
- Block all (or most) extensions from touching Intranet pages to reduce the threat of data leaks ( runtime_blocked_hosts policy).
- Guide all Intranet navigations into an appropriate profile or container (a la Detangle ).
- Upstream , there’s a longstanding desire to help protect intranets/local machine from cross-site-request-forgery attacks; blocking loads and navigations of private resources from the Internet Zone is somewhat simpler than blocking them from Intranet Sites. The current plan is to protect RFC1918-reserved address space .
At present, only AutoSelectCertificateForUrls , AutoOpenFileTypes, AutoLaunchProtocolsFromOrigins . manual cookie controls, and mixed content nags support policy-pushed site lists, but their list syntax doesn’t have any concept of “the entire Intranet” (all dotless hosts, hosts that bypass proxy).
You’ll notice that each of these has potential security impact (e.g. an XSS on a privileged “Intranet” page becomes more dangerous; unqualified hostnames can result in name collisions ), but having the ability to scope some powerful features to only “Intranet” sites might also improve security by reducing attack surface.
As browser designers, we must weigh the enterprise impact of every change we make, and being able to say “ This won’t apply to your intranet if you don’t want it to ” would be very liberating. Unfortunately, building such an escape hatch is also the recipe for accumulating technical debt and permitting the corporate intranets to “rust” to the point that they barely resemble the modern public web.
Best Practices
Throughout Chromium, many features are designed respect an individual policy-pushed list of sites to control their behavior. If you were forward-thinking enough to structure your intranet such that your hostnames are of the form:
- https://payroll. contoso-intranet.com
- https://timecard. contoso-intranet.com
- https://sharepoint. contoso-intranet.com
…Congratulations, you’ve lucked into a best practice. You can configure each desired policy with a *.contoso-intranet.com entry and your entire Intranet will be opted in.
Unfortunately, while wildcards are supported, there’s presently no way to express the concept of “any dotless hostname.”
Why is that unfortunate? For over twenty years, Internet Explorer and legacy Edge mapped domain names like https://payroll , https://timecard , and https://sharepoint/ to the Intranet Zone by default. As a result, many smaller companies have benefitted from this simple heuristic that requires no configuration changes by the user or the IT department.
Opportunity: Maybe such a DOTLESS_HOSTS token should exist in the Chromium policy syntax. This seems unlikely to happen. Edge has been on Chromium for over two years now, and there’s no active plan to introduce such a feature.
- Internet Explorer and Legacy Edge use a system of five Zones and 88+ URLActions to make security decisions for web content, based on the host of a target site.
- Chromium (New Edge, Chrome) uses a system of Site Lists and permission checks to make security decisions for web content, based on the hostname of a target site.
There does not exist an exact mapping between these two systems, which exist for similar reasons but implemented using very different mechanisms.
In general, users should expect to be able to use the new Edge without configuring anything; many of the URLActions that were exposed by IE/Spartan have no logical equivalent in modern browsers.
If the new Edge browser does not behave in the desired way for some customer scenario, then we must examine the details of what isn’t working as desired to determine whether there exists a setting (e.g. a Group Policy-pushed SiteList) that provides the desired experience.
1 Technically, it was possible for an administrator to create “Custom Security Zones” (with increasing ZoneIds starting at #5), but such a configuration has not been officially supported for at least fifteen years, and it’s been a periodic source of never-will-be-fixed bugs.
2 Beyond those explicit uses of Windows’ Zone Manager, various components in Chromium have special handling for localhost/loopback addresses, and some have special recognition of RFC1918 private IP Address ranges, e.g. SafeBrowsing handling, navigation restrictions, and Network Quality Estimation. As of 2022, Chrome did a big refactor to allow determination of whether or not the target site’s IP address is in the public IP Address space or the private IP address space (e.g. inherently Intranet) as a part of the Private Network Access spec . This check should now be basically free (it’s getting used on every resource load) and it may make sense to start using it in a lot of places to approximate the “ This target is not on the public Internet ” check. Within Edge, the EMIE List is another mechanism by which sites’ hostnames may result in different handling.
Ancient History
Security Zones were introduced with Internet Explorer 4, released back in 1997:
The UI has only changed a little bit since that time, with most of the changes happening in IE5. There were only tiny tweaks in IE6, 7, and 8.
Share this:
Published by ericlaw.
Impatient optimist. Dad. Author/speaker. Created Fiddler & SlickRun. PM @ Microsoft 2001-2012, and 2018-, working on Office, IE, and Edge. Now a GPM for Microsoft Defender. My words are my own, I do not speak for any other entity. View more posts
2 thoughts on “ Security Zones in Edge ”
In IE it is possible to see which zone is active on a page you’re currently viewing (alt to show menu bar, -> file -> properties).
Is it possible to see this in the new Edge?
No, although as noted, the Zone isn’t used for very much. To see the Zone, you’d have to reload the same page in IE (or use a command line utility or similar).
Leave a comment Cancel reply
- Already have a WordPress.com account? Log in now.
- Subscribe Subscribed
- Copy shortlink
- Report this content
- View post in Reader
- Manage subscriptions
- Collapse this bar

an endpoint admin's journal
- Recent Posts
- Popular Posts
- Recent Comments

Deploy Trusted sites zone assignment using Intune
November 6, 2023

Zoom Desktop Client – Download older build versions from Zoom
October 31, 2023

Uninstall Teams chat app using remediation script and a configuration profile in Intune
October 30, 2023

Intune Last Check-in date not updating for Windows device
October 25, 2023

How to use Event Viewer to check cause of Blue screen of Death (BSOD)
October 23, 2023
5 Quick Mac OS Terminal commands to make a Mac user life easier

Powershell : Find disabled users and computers in AD
- Active Directory (1)
- Windows (7)
- November 2023
- October 2023
Deploy a set of trusted sites overriding users’ ability to add trusted sites themselves. To acheive this, an Intune configuration profile Trusted site zone assignment can be deployed to devices/users group as required.
Login to Intune Portal and navigate to: Devices > Windows > Configuration Profiles .
Hit the Create button and Select New policy

From the Create a profile menu, select Windows 10 and later for Platform , Templates for Profile type. Select Administrative templates and click Create .

Give the profile desired name and click Next .

In Configurations settings, select Computer Configuration and search for keyword “ Site to Zone “, Site to Zone Assignment List setting will be listed under search results. Go ahead click on it to Select it.

Once selected, a Site to Zone Assignment List page will appear on right side explaining different zones and values required for these zone for setup. Since this profile is being used for trusted sites, we will use the Value “2” . Go ahead and select Enabled button and start entering the trusted sites as required. please ensure to set each value to “2” . See example below:
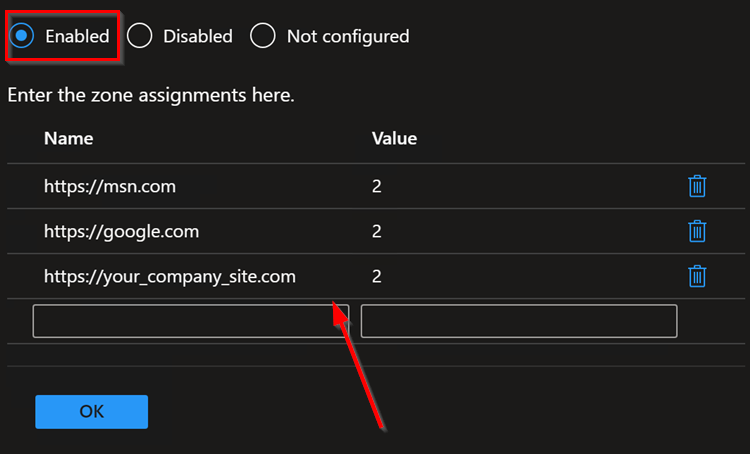
Once done adding the list of sites, click OK to close it and Hit Next on Configuration settings page.
Add Scope tags if needed.
Under Assignments , Click Add groups to target the policy deployment to specific group of devices/users. You can also select Add all users / All all devices .
Hit Next . Then Hit Review + Save button to save.
Tags: Intune Windows
You may also like...

[Windows 10] How to completely uninstall Flash player

- Previous Zoom Desktop Client – Download older build versions from Zoom
thanks! I was just looking for this exact solution!
The Federal Register
The daily journal of the united states government, request access.
Due to aggressive automated scraping of FederalRegister.gov and eCFR.gov, programmatic access to these sites is limited to access to our extensive developer APIs.
If you are human user receiving this message, we can add your IP address to a set of IPs that can access FederalRegister.gov & eCFR.gov; complete the CAPTCHA (bot test) below and click "Request Access". This process will be necessary for each IP address you wish to access the site from, requests are valid for approximately one quarter (three months) after which the process may need to be repeated.
An official website of the United States government.
If you want to request a wider IP range, first request access for your current IP, and then use the "Site Feedback" button found in the lower left-hand side to make the request.

IMAGES
VIDEO
COMMENTS
Open Group Policy Management Console. Navigate to the desired GPO or create a new one. Expand User Configuration or Computer Configuration and go to Preferences -> Windows Settings -> Registry. Right-click and select New -> Registry Item. Configure the Registry Item to delete the specified entries under the ZoneMap registry key.
Step 2. Navigate to User Configuration > Administrative Templates > Windows Components > Internet Explorer > Internet Control Panel > Security Page and double click on the “Site to Zone Assignment List†and check the “Enable†option then click on the “Show..†button. Step 3.
In the main pane, double-click the Sites to Zone Assignment List setting. Enable the Group Policy setting by selecting the Enabled option in the top pane. Click the Show ... Add Site to Local Intranet Zone Group Policy. Posted on October 17, 2019 by Sander Berkouwer in Active Directory, Entra ID, Security.
In managed environments, administrators can use Group Policy to assign specific sites to Zones (via "Site to Zone Assignment List" policy) and specify the settings for URLActions on a per-zone basis. Beyond manual administrative or user assignment of sites to Zones, other heuristics could assign sites to the Local Intranet Zone .
In the main pane, double-click the Sites to Zone Assignment List setting. Enable the Group Policy setting by selecting the Enabled option in the top pane. Click the Show ... Add Site to Local Intranet Zone Group Policy. Posted on October 15, 2019 by Sander Berkouwer in Active Directory, Entra ID, Security.
Re: Site to Zone Assignment List - Powershell. # Step 2: Navigate to the Site to Zone Assignment List # This step is manual and requires navigating through the Group Policy Management Editor interface. # Step 3: Enable the Policy and Specify Zone Assignments # Define the list of URLs and their corresponding zone assignments.
As you can see below the IE zone will push out to your users and it will be added to the trusted zone list, while still allowing them to add and remove other zones from the list. TIP: As always the native group policy settings will take precedence over Group Policy Preferences therefore if you have the "Site to Zone Assignment List" setting ...
1 - Intranet Zone; 2 - Trusted Sites Zone; 3 - Internet Zone; 4 - Restricted Sites Zone; Once the zone assignment has been entered, click "OK". This will once again show the "Show Contents" window and the new entry should be present. Click "OK" and "OK" again to get back to the Group Policy Management Console. The new ...
Figure 1. Assigning sites to the Trusted Sites zone. Figure 2. Enabling the Site to Zone Assignment List policy. By enabling this policy setting, you can manage a list of sites that you want to associate with a particular security zone. See Figure 2. Restricting users from changing security zone policies. Open the Group Policy Management Editor.
When possible, use the computer configuration option as it will not impact user logons. When you enable the setting, you will be prompted for a value name (the website) and a value (the zone list). Here are the possible values and the zone that they correspond to: 1 = Intranet/Local Zone. 2 = Trusted Sites. 3 = Internet/Public Zone.
Control panel > internet options > trusted sites. rod-it (Rod-IT) September 8, 2022, 2:39pm 3. GPO. Computer Configuration — Administrative Tools — Windows Components — Internet Explorer — Internet Control Panel — Security Page and then double click to the "Site to zone assignment list". bryancomanici (bcomanici) September 13 ...
If you want to lock it down and add as needed, GPO will work just fine, just go to Win Components/Internet Explorer/Internet Control Panel/Security Page - Site to Zone Assignment - enable the policy, click List and add the sites as needed, a value of 1 is Intranet a value of 2 would be Trusted. Yes. I want to lock it down so I will do it in ...
I created a new user account, and when logged on for the first time, it too experienced the same issue with sites not showing in IE, even though the GPO was applied. I found in HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap , there is a key called IEHarden (remembered the name back from my 2003 days with a ...
Double-click the "Site to Zone Assignment List" entry, check the enabled button, then click the "show" button. ... 2 = Trusted Sites Zone 3 = Internet Zone 4 = Restricted Sites Zone. Once you have created your list and zones just apply the GPO to the OU, refresh the policy which will grey-out the option for the user to modify and you ...
Internet Explorer security zones settings are stored under the following registry subkeys: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings. HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings. These registry keys contain the following keys: TemplatePolicies. ZoneMap.
1. Find the setting. Use Group Policy Management console to locate one of these settings below: User Configuration > Preferences > Windows Settings > Registry = With this way, the site zone mapping will follow the user on any computer it is logged in to. Computer Configuration > Preferences > Windows Settings > Registry = With this way, the ...
In corporate or other managed environments, administrators can use Group Policy to assign specific sites to Zones (via "Site to Zone Assignment List" policy) and specify the settings for URLActions on a per-zone basis. ... Beyond manual administrative or user assignment of sites to Zones, the platform used additional heuristics that could ...
For example, I have a list with two entries named like following. https://something.domain.local. https://something.domain.local:123. After some quick googling I found out that some are saying that while the list is being processed, it just strippes out the port. Which I now assume, I could just go with the first entry in the list and delete ...
Deploy a set of trusted sites overriding users' ability to add trusted sites themselves. To acheive this, an Intune configuration profile Trusted site zone assignment can be deployed to devices/users group as required. Login to Intune Portal and navigate to: Devices > Windows > Configuration Profiles. Hit the Create button and Select New ...
Manage Google Chrome using Group Policy, SCCM or your own management utility. On-Demand Demo. PolicyPak Least Privilege Manager v. Traditional Whitelisting (such as Applocker) ... Why doesn't Site to Zone list assignment work with the syntax I provided? Posted on December 18, 2020 by Ali Hassan.
There is a GPO which gathers information about all PCes, this GPO also sets the following in the "Site to Zone Assignment List, Local Intranet": -Both domaincontrollers -The fileserver The question is; should domain controllers be in this list? Should the fileserver be in this list? I tested disabling this GPO for a couple weeks.
This site displays a prototype of a "Web 2.0" version of the daily Federal Register. It is not an official legal edition of the Federal Register, and does not replace the official print version or the official electronic version on GPO's govinfo.gov. The documents posted on this site are XML renditions of published Federal Register ...